Configurando a sessão PPPoE de uma máquina Windows para um roteador Cisco
Opções de download
Linguagem imparcial
O conjunto de documentação deste produto faz o possível para usar uma linguagem imparcial. Para os fins deste conjunto de documentação, a imparcialidade é definida como uma linguagem que não implica em discriminação baseada em idade, deficiência, gênero, identidade racial, identidade étnica, orientação sexual, status socioeconômico e interseccionalidade. Pode haver exceções na documentação devido à linguagem codificada nas interfaces de usuário do software do produto, linguagem usada com base na documentação de RFP ou linguagem usada por um produto de terceiros referenciado. Saiba mais sobre como a Cisco está usando a linguagem inclusiva.
Sobre esta tradução
A Cisco traduziu este documento com a ajuda de tecnologias de tradução automática e humana para oferecer conteúdo de suporte aos seus usuários no seu próprio idioma, independentemente da localização. Observe que mesmo a melhor tradução automática não será tão precisa quanto as realizadas por um tradutor profissional. A Cisco Systems, Inc. não se responsabiliza pela precisão destas traduções e recomenda que o documento original em inglês (link fornecido) seja sempre consultado.
Contents
Introduction
Este documento descreve o procedimento para configurar uma conexão ponto a ponto sobre Ethernet (PPPoE) entre uma máquina Windows (que atua como um cliente PPPoE) e um roteador Cisco que atua como um servidor PPPoE.
Prerequisites
Requirements
A Cisco recomenda que você tenha conhecimento de que a conectividade de ponta a ponta da camada 1 é a UP (User Priority, Prioridade de usuário).
Componentes Utilizados
Este documento não se restringe a versões de software e hardware específicas.
The information in this document was created from the devices in a specific lab environment. All of the devices used in this document started with a cleared (default) configuration. If your network is live, make sure that you understand the potential impact of any command.
Configurar
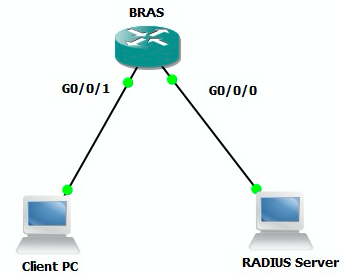
Diagrama de Rede
Este documento usa a configuração de rede mostrada na imagem:
Configurações
Configuração BRAS
aaa new-model ! Enabling AAA on router ! aaa authentication ppp PPPOE-METD group PPPOE-RADIUS ! Defining AAA method list for PPP Authentication aaa authorization network PPPOE-AUTHOR-METD group PPPOE-RADIUS ! Defining AAA method list for PPP Authorization aaa accounting network PPPOE-ACCT-METD start-stop group PPPOE-RADIUS ! Defining AAA method list for PPP Accounting ! aaa group server radius PPPOE-RADIUS ! Defining AAA Server Group named PPPOE-RADIUS server-private 10.106.39.253 key cisco ip radius source-interface GigabitEthernet0/0/0 ! bba-group pppoe BBA-TEST virtual-template 10 ! interface GigabitEthernet0/0/1.47 encapsulation dot1Q 1 native pppoe enable group BBA-TEST end ! interface Virtual-Template10 ip unnumbered Loopback10 peer default ip address pool local ! Calling three named AAA Method lists configured above under this Virtual Template ppp authentication pap chap PPPOE-METD ppp authorization PPPOE-AUTHOR-METD ppp accounting PPPOE-ACCT-METD end ! ip local pool local 192.168.1.2 192.168.1.10 ! interface Loopback10 ip address 192.168.1.1 255.255.255.255 end !
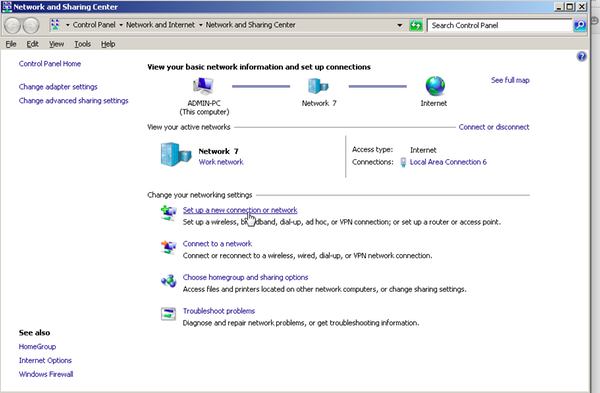
Configurações e configurações da máquina Windows
Conclua estes passos para iniciar a sessão PPPoE a partir da Máquina Windows que atua como um Cliente PPPoE.
Etapa 1. Abra a Central de Rede e Compartilhamento e clique em Configurar uma nova conexão ou rede conforme mostrado na imagem.
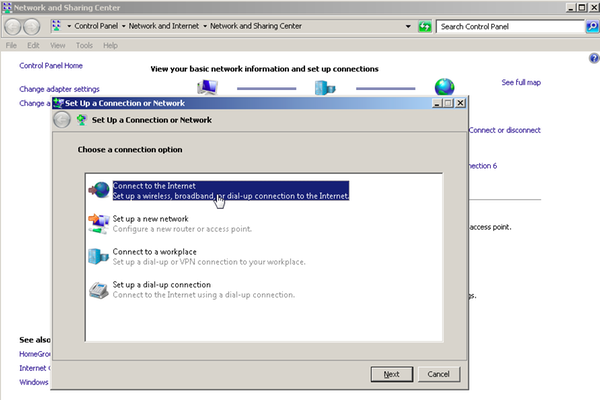
Etapa 2. Como mostrado na imagem, selecione Conectar-se à Internet e clique em Avançar.
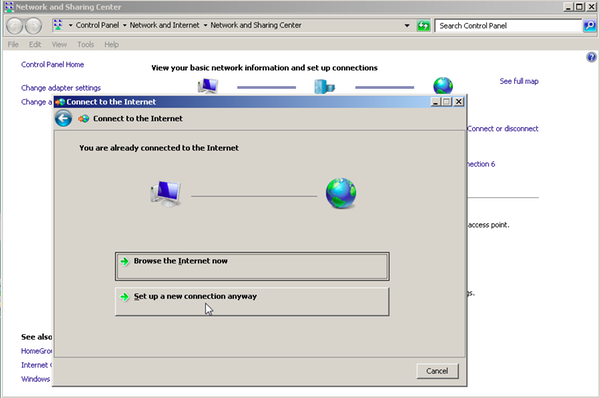
Etapa 3. Selecione Configurar uma nova conexão mesmo assim, como mostrado na imagem:
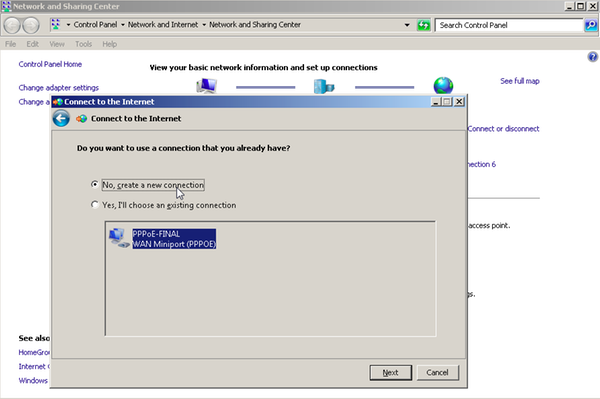
Etapa 4. Selecione Não, crie uma nova conexão, como mostrado na imagem:
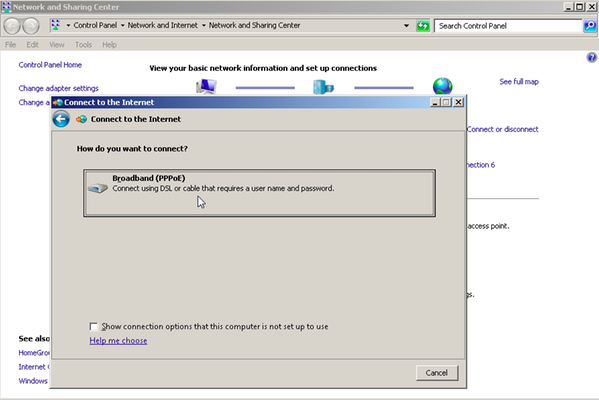
Etapa 5. Como mostrado na imagem, clique em Banda larga (PPPoE):
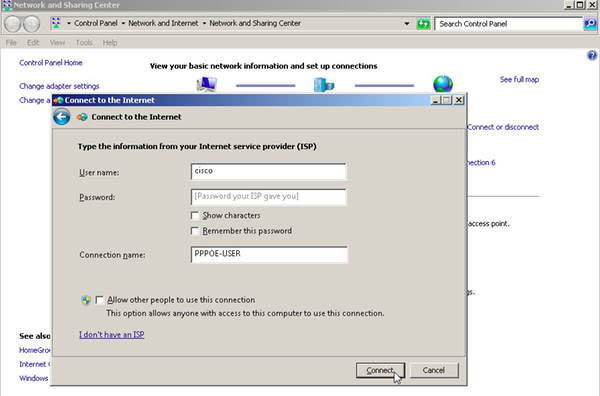
Etapa 6. Como mostrado na imagem, insira o nome de usuário, a senha e um nome de conexão e clique em CONNECT.
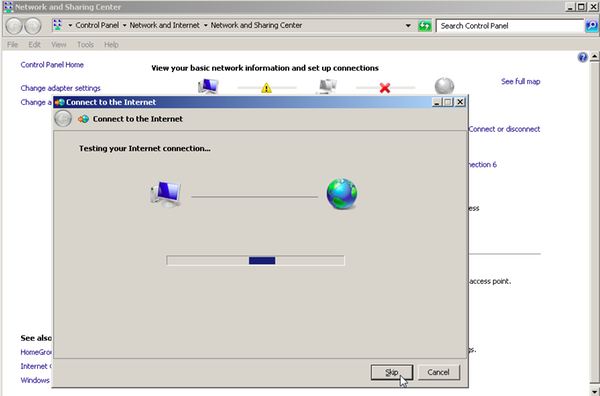
Isso inicia uma sessão PPPoE para o servidor. Verifique a seção de verificação como mostrado na imagem:
Verificar
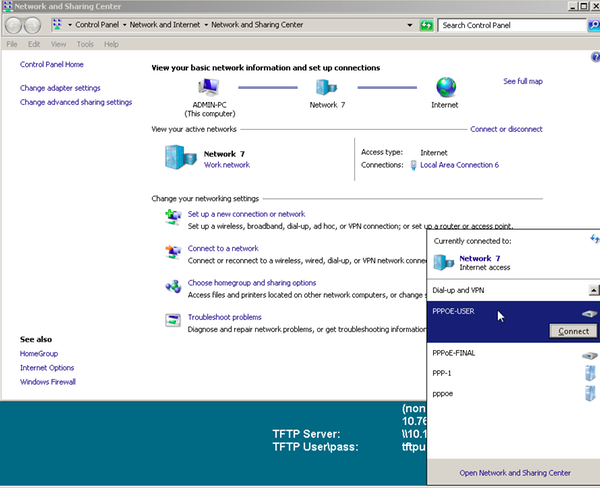
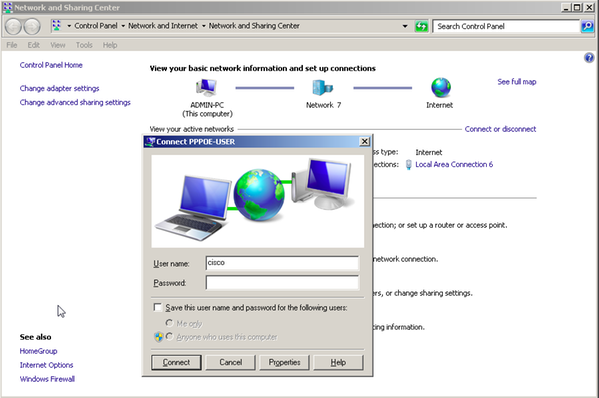
Etapa 1. Abra novamente a guia Redes,selecione a rede (neste exemplo, PPPOE-USER) e verifique o status. Clique em Connect para iniciar uma sessão depois de inserir o nome de usuário e a senha, conforme mostrado na imagem:
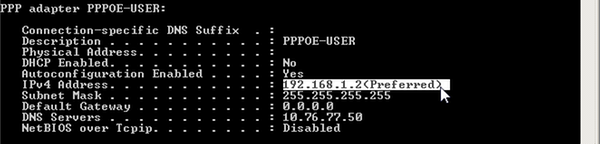
Etapa 2. Abra o prompt de comando e execute o comando ipconfig /all para verificar o endereço IP negociado, como mostrado na imagem:
Etapa 3. Ative debug pppoe event, debug pppoe error e debug ppp negotiation para verificar o estabelecimento da sessão PPPoE. Também podemos habilitar o debug radius para ver as mensagens trocadas com o servidor Radius.
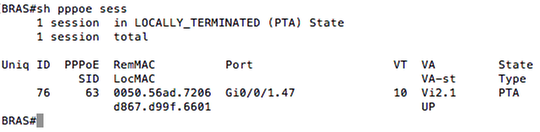
BRAS#show debugging PPP: PPP protocol negotiation debugging is on PPPoE: PPPoE protocol events debugging is on PPPoE protocol errors debugging is on Radius protocol debugging is on Radius packet protocol debugging is on Debug snippet: BRAS# *Sep 19 18:44:14.531: PPPoE 0: I PADI R:0050.56ad.7206 L:ffff.ffff.ffff Gi0/0/1.47 ! Receiving PPPoE Active Discovery Initiation (PADI) broadcast packet from Windows Machine (MAC 0050.56ad.7206) on Router interface Gi0/0/1.47 *Sep 19 18:44:14.531: Service tag: NULL Tag *Sep 19 18:44:14.531: PPPoE 0: O PADO, R:d867.d99f.6601 L:0050.56ad.7206 Gi0/0/1.47 ! Sending PPPoE Active Discovery Offer (PADO) unicast packet from Router interface Gi0/0/1.47 (MAC d867.d99f.6601 ) to Windows Machine (MAC 0050.56ad.7206) *Sep 19 18:44:14.531: Service tag: NULL Tag *Sep 19 18:44:14.533: PPPoE 0: I PADR R:0050.56ad.7206 L:d867.d99f.6601 Gi0/0/1.47 ! Receiving PPPoE Active Discovery Request (PADR) unicast packet from Windows Machine (MAC 0050.56ad.7206) on Router interface Gi0/0/1.47 *Sep 19 18:44:14.533: Service tag: NULL Tag *Sep 19 18:44:14.533: PPPoE : encap string prepared *Sep 19 18:44:14.533: [76]PPPoE 63: Access IE handle allocated *Sep 19 18:44:14.533: [76]PPPoE 63: AAA get retrieved attrs *Sep 19 18:44:14.533: [76]PPPoE 63: AAA get nas port details *Sep 19 18:44:14.533: [76]PPPoE 63: Error adjusting nas port format did *Sep 19 18:44:14.533: [76]PPPoE 63: AAA get dynamic attrs *Sep 19 18:44:14.533: [76]PPPoE 63: AAA unique ID 88 allocated *Sep 19 18:44:14.533: [76]PPPoE 63: No AAA accounting method list *Sep 19 18:44:14.534: [76]PPPoE 63: Service request sent to SSS *Sep 19 18:44:14.534: [76]PPPoE 63: Created, Service: None R:d867.d99f.6601 L:0050.56ad.7206 Gi0/0/1.47 *Sep 19 18:44:14.534: [76]PPPoE 63: State NAS_PORT_POLICY_INQUIRY Event SSS MORE KEYS *Sep 19 18:44:14.534: PPP: Alloc Context [7FE79EC0D8C8] *Sep 19 18:44:14.534: ppp76 PPP: Phase is ESTABLISHING *Sep 19 18:44:14.534: [76]PPPoE 63: data path set to PPP *Sep 19 18:44:14.534: [76]PPPoE 63: Segment (SSS class): PROVISION ! We can also enable 'debug sss events' and 'debug sss error' to debug this stage *Sep 19 18:44:14.534: [76]PPPoE 63: State PROVISION_PPP Event SSM PROVISIONED *Sep 19 18:44:14.534: [76]PPPoE 63: O PADS R:0050.56ad.7206 L:d867.d99f.6601 Gi0/0/1.47 ! Sending PPPoE Active Discovery Session Confirmation (PADS) unicast packets from Router interface Gi0/0/1.47 (MAC d867.d99f.6601 ) to Windows Machine (MAC 0050.56ad.7206) *Sep 19 18:44:14.534: [76]PPPoE 63: Unable to Add ANCP Line attributes to the PPPoE Authen attributes ! Access Node Control Protocol (ANCP) is configured between the Digital Subscriber Line Access Concentrator (DSLAM) and Broadband Remote Access Server (BRAS), which is used to aggregate traffic from multiple subscribers and deliver information for any application independently. More information related to ANCP could be found here. It is expected for the IOS to print this message even if ANCP is not enabled. *Sep 19 18:44:14.534: ppp76 PPP: Using vpn set call direction *Sep 19 18:44:14.534: ppp76 PPP: Treating connection as a callin *Sep 19 18:44:14.534: ppp76 PPP: Session handle[8800004C] Session id[76] *Sep 19 18:44:14.534: ppp76 LCP: Event[OPEN] State[Initial to Starting] *Sep 19 18:44:14.534: ppp76 PPP LCP: Enter passive mode, state[Stopped] *Sep 19 18:44:14.539: ppp76 LCP: I CONFREQ [Stopped] id 0 len 21 *Sep 19 18:44:14.539: ppp76 LCP: MRU 1480 (0x010405C8) *Sep 19 18:44:14.539: ppp76 LCP: MagicNumber 0x61EB5A46 (0x050661EB5A46) *Sep 19 18:44:14.539: ppp76 LCP: PFC (0x0702) *Sep 19 18:44:14.539: ppp76 LCP: ACFC (0x0802) *Sep 19 18:44:14.539: ppp76 LCP: Callback 6 (0x0D0306) *Sep 19 18:44:14.539: ppp76 LCP: O CONFREQ [Stopped] id 1 len 18 *Sep 19 18:44:14.539: ppp76 LCP: MRU 1492 (0x010405D4) *Sep 19 18:44:14.539: ppp76 LCP: AuthProto PAP (0x0304C023) *Sep 19 18:44:14.539: ppp76 LCP: MagicNumber 0x7B063BEA (0x05067B063BEA) *Sep 19 18:44:14.539: ppp76 LCP: O CONFREJ [Stopped] id 0 len 7 *Sep 19 18:44:14.539: ppp76 LCP: Callback 6 (0x0D0306) *Sep 19 18:44:14.539: ppp76 LCP: Event[Receive ConfReq-] State[Stopped to REQsent] *Sep 19 18:44:14.540: ppp76 LCP: I CONFACK [REQsent] id 1 len 18 *Sep 19 18:44:14.540: ppp76 LCP: MRU 1492 (0x010405D4) *Sep 19 18:44:14.540: ppp76 LCP: AuthProto PAP (0x0304C023) *Sep 19 18:44:14.540: ppp76 LCP: MagicNumber 0x7B063BEA (0x05067B063BEA) *Sep 19 18:44:14.540: ppp76 LCP: Event[Receive ConfAck] State[REQsent to ACKrcvd] *Sep 19 18:44:14.540: ppp76 LCP: I CONFREQ [ACKrcvd] id 1 len 18 *Sep 19 18:44:14.540: ppp76 LCP: MRU 1480 (0x010405C8) *Sep 19 18:44:14.540: ppp76 LCP: MagicNumber 0x61EB5A46 (0x050661EB5A46) *Sep 19 18:44:14.540: ppp76 LCP: PFC (0x0702) *Sep 19 18:44:14.540: ppp76 LCP: ACFC (0x0802) *Sep 19 18:44:14.540: ppp76 LCP: O CONFACK [ACKrcvd] id 1 len 18 *Sep 19 18:44:14.540: ppp76 LCP: MRU 1480 (0x010405C8) *Sep 19 18:44:14.540: ppp76 LCP: MagicNumber 0x61EB5A46 (0x050661EB5A46) *Sep 19 18:44:14.540: ppp76 LCP: PFC (0x0702) *Sep 19 18:44:14.540: ppp76 LCP: ACFC (0x0802) *Sep 19 18:44:14.540: ppp76 LCP: Event[Receive ConfReq+] State[ACKrcvd to Open] *Sep 19 18:44:14.541: ppp76 LCP: I IDENTIFY [Open] id 2 len 18 magic 0x61EB5A46MSRASV5.20 *Sep 19 18:44:14.541: ppp76 LCP: I IDENTIFY [Open] id 3 len 24 magic 0x61EB5A46MSRAS-0-ADMIN-PC *Sep 19 18:44:14.541: ppp76 LCP: I IDENTIFY [Open] id 4 len 24 magic 0x61EB5A46sPPY.X`I?Z5SWE}} *Sep 19 18:44:14.541: ppp76 PPP: Queue PAP code[1] id[78] *Sep 19 18:44:14.563: ppp76 PPP: Phase is AUTHENTICATING, by this end *Sep 19 18:44:14.564: ppp76 PAP: Redirect packet to ppp76 *Sep 19 18:44:14.564: ppp76 PAP: I AUTH-REQ id 78 len 11 from "cisco" ! Incoming Authentication Request from Windows Machine using User name "cisco" *Sep 19 18:44:14.564: ppp76 PAP: Authenticating peer cisco *Sep 19 18:44:14.564: ppp76 PPP: Phase is FORWARDING, Attempting Forward *Sep 19 18:44:14.564: ppp76 LCP: State is Open *Sep 19 18:44:14.564: ppp76 PPP: Phase is AUTHENTICATING, Unauthenticated User *Sep 19 18:44:14.564: RADIUS/ENCODE(00000088):Orig. component type = PPPoE *Sep 19 18:44:14.564: RADIUS: DSL line rate attributes successfully added *Sep 19 18:44:14.564: RADIUS/ENCODE: Skip encoding 0 length AAA Cisco vsa password *Sep 19 18:44:14.564: RADIUS(00000088): Config NAS IP: 10.106.39.212 *Sep 19 18:44:14.564: RADIUS(00000088): Config NAS IPv6: :: *Sep 19 18:44:14.564: RADIUS/ENCODE: No idb found! Framed IP Addr might not be included *Sep 19 18:44:14.564: RADIUS/ENCODE(00000088): acct_session_id: 125 *Sep 19 18:44:14.564: RADIUS(00000088): Config NAS IP: 10.106.39.212 *Sep 19 18:44:14.564: RADIUS(00000088): sending *Sep 19 18:44:14.564: RADIUS(00000088): Send Access-Request to 10.106.39.253:1645 id 1645/106, len 147 ! Sending an Access-Request to Radius Server at 10.106.39.253 on port 1645. *Sep 19 18:44:14.564: RADIUS: authenticator C1 5B AA 62 1D E1 31 6C - 16 A5 CE 92 D6 9C 12 E7 *Sep 19 18:44:14.564: RADIUS: Framed-Protocol [7] 6 PPP [1] *Sep 19 18:44:14.564: RADIUS: User-Name [1] 7 "cisco" *Sep 19 18:44:14.564: RADIUS: User-Password [2] 18 * *Sep 19 18:44:14.564: RADIUS: NAS-Port-Type [61] 6 Virtual [5] *Sep 19 18:44:14.564: RADIUS: NAS-Port [5] 6 0 *Sep 19 18:44:14.564: RADIUS: NAS-Port-Id [87] 9 "0/0/1/1" *Sep 19 18:44:14.564: RADIUS: Vendor, Cisco [26] 41 *Sep 19 18:44:14.564: RADIUS: Cisco AVpair [1] 35 "client-mac-address=0050.56ad.7206" *Sep 19 18:44:14.564: RADIUS: Service-Type [6] 6 Framed [2] *Sep 19 18:44:14.564: RADIUS: NAS-IP-Address [4] 6 10.106.39.212 *Sep 19 18:44:14.564: RADIUS: Acct-Session-Id [44] 10 "0000007D" *Sep 19 18:44:14.564: RADIUS: Nas-Identifier [32] 12 "BRAS" *Sep 19 18:44:14.564: RADIUS(00000088): Sending a IPv4 Radius Packet *Sep 19 18:44:14.564: RADIUS(00000088): Started 5 sec timeout *Sep 19 18:44:14.566: RADIUS: Received from id 1645/106 10.106.39.253:1645, Access-Accept, len 52 ! Receiving an Access-Accep from Radius Server *Sep 19 18:44:14.566: RADIUS: authenticator C0 0D 6C 33 F1 A3 04 27 - F0 C2 76 F5 54 FD E2 42 *Sep 19 18:44:14.566: RADIUS: Class [25] 32 *Sep 19 18:44:14.566: RADIUS: 4A 83 05 60 00 00 01 37 00 01 0A 6A 27 FD 01 D2 12 2E 98 D0 4F B0 00 00 00 00 00 00 00 14 [ J`7j'.O] *Sep 19 18:44:14.566: RADIUS(00000088): Received from id 1645/106 *Sep 19 18:44:14.566: ppp76 PPP: Phase is FORWARDING, Attempting Forward *Sep 19 18:44:14.568: [76]PPPoE 63: State LCP_NEGOTIATION Event SSS CONNECT LOCAL *Sep 19 18:44:14.568: [76]PPPoE 63: Segment (SSS class): UPDATED *Sep 19 18:44:14.568: [76]PPPoE 63: Segment (SSS class): BOUND *Sep 19 18:44:14.568: [76]PPPoE 63: data path set to Virtual Acess *Sep 19 18:44:14.569: [76]PPPoE 63: State LCP_NEGOTIATION Event SSM UPDATED *Sep 19 18:44:14.569: Vi2.1 PPP: Phase is AUTHENTICATING, Authenticated User *Sep 19 18:44:14.569: Vi2.1 PAP: O AUTH-ACK id 78 len 5 *Sep 19 18:44:14.569: Vi2.1 PPP: Reducing MTU to peer's MRU *Sep 19 18:44:14.569: [76]PPPoE 63: AAA get dynamic attrs *Sep 19 18:44:14.569: Vi2.1 PPP: Phase is UP *Sep 19 18:44:14.569: Vi2.1 IPCP: Protocol configured, start CP. state[Initial] *Sep 19 18:44:14.569: Vi2.1 IPCP: Event[OPEN] State[Initial to Starting] *Sep 19 18:44:14.569: Vi2.1 IPCP: O CONFREQ [Starting] id 1 len 10 *Sep 19 18:44:14.569: Vi2.1 IPCP: Address 192.168.1.1 (0x0306C0A80101) *Sep 19 18:44:14.569: Vi2.1 IPCP: Event[UP] State[Starting to REQsent] *Sep 19 18:44:14.569: [76]PPPoE 63: State PTA_BINDING Event STATIC BIND RESPONSE *Sep 19 18:44:14.569: [76]PPPoE 63: Connected PTA <snip> *Sep 19 18:44:14.572: Vi2.1 IPCP: Event[Receive ConfReq+] State[ACKrcvd to Open] *Sep 19 18:44:14.595: Vi2.1 IPCP: State is Open *Sep 19 18:44:14.595: PPPoE : ipfib_encapstr prepared *Sep 19 18:44:14.596: Vi2.1 Added to neighbor route AVL tree: topoid 0, address 192.168.1.2 *Sep 19 18:44:14.596: Vi2.1 IPCP: Install route to 192.168.1.2 ! Installing route to PPPoE client
BRAS#sh caller ip Line User IP Address Local Number Remote Number <-> Vi2.1 cisco 192.168.1.2 - - in BRAS# ping 192.168.1.2 Type escape sequence to abort. Sending 5, 100-byte ICMP Echos to 192.168.1.2, timeout is 2 seconds: !!!!! Success rate is 100 percent (5/5), round-trip min/avg/max = 1/1/1 ms
Troubleshoot
Atualmente, não existem informações disponíveis específicas sobre Troubleshooting para esta configuração. Entretanto, podemos aplicar técnicas padrão de solução de problemas relacionados ao PPP e PPPoE com a ajuda de depurações relacionadas.
Informações Relacionadas
Colaborado por engenheiros da Cisco
- Utsav DuttCisco TAC Engineer
Contate a Cisco
- Abrir um caso de suporte

- (É necessário um Contrato de Serviço da Cisco)
 Feedback
Feedback