Configuración de DVTI con protocolos de routing dinámico en firewall seguro
Lenguaje no discriminatorio
El conjunto de documentos para este producto aspira al uso de un lenguaje no discriminatorio. A los fines de esta documentación, "no discriminatorio" se refiere al lenguaje que no implica discriminación por motivos de edad, discapacidad, género, identidad de raza, identidad étnica, orientación sexual, nivel socioeconómico e interseccionalidad. Puede haber excepciones en la documentación debido al lenguaje que se encuentra ya en las interfaces de usuario del software del producto, el lenguaje utilizado en función de la documentación de la RFP o el lenguaje utilizado por un producto de terceros al que se hace referencia. Obtenga más información sobre cómo Cisco utiliza el lenguaje inclusivo.
Acerca de esta traducción
Cisco ha traducido este documento combinando la traducción automática y los recursos humanos a fin de ofrecer a nuestros usuarios en todo el mundo contenido en su propio idioma. Tenga en cuenta que incluso la mejor traducción automática podría no ser tan precisa como la proporcionada por un traductor profesional. Cisco Systems, Inc. no asume ninguna responsabilidad por la precisión de estas traducciones y recomienda remitirse siempre al documento original escrito en inglés (insertar vínculo URL).
Contenido
Introducción
Este documento describe cómo configurar una Interfaz de túnel virtual dinámico (DVTI) en Secure Firewall 9.20.
Prerequisites
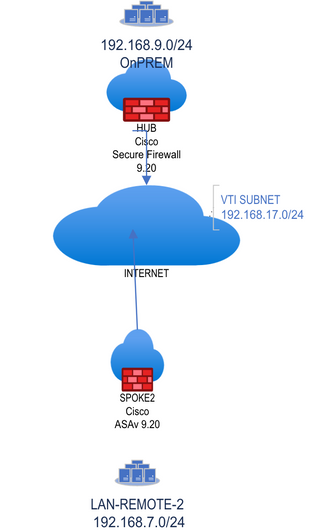
- Disponga de un Cisco Secure Firewall con ASA 9.20 o posterior con una configuración de routing básica y compatibilidad con IKEV2 que funcione como concentrador con una interfaz de bucle invertido para simular la red local en las instalaciones de 192.168.9.0/24.
- Disponga de un Cisco Secure Firewall con ASA 9.20 o posterior con configuración de routing básica y compatibilidad con IKEv2 para funcionar como spoke-1 con una interfaz de bucle invertido preconfigurada para simular una red remota de 192.168.7.0/24.
Requirements
- Conocimiento general de todos los protocolos de ruteo dinámico descritos en este documento (OSPF, EIGRP y BGP).
- Familiarícese con la configuración de CLI en los dispositivos Cisco Secure Firewall.
Componentes Utilizados
La información que contiene este documento se basa en estas versiones de software:
- Cisco Secure Firewall con ASA 9.20 o posterior.

Nota: La información de este documento se creó a partir de los dispositivos de un entorno de laboratorio específico. Todos los dispositivos que se utilizan en este documento se pusieron en funcionamiento con una configuración verificada (predeterminada). Si tiene una red en vivo, asegúrese de entender el posible impacto de cualquier comando.
Antecedentes
Interfaces de Túnel Virtuales Dinámicas
Las interfaces de túnel virtual (DVTI) dinámicas pueden proporcionar una conectividad muy segura y escalable para redes privadas virtuales (VPN) de acceso remoto.
Las DVTI se pueden utilizar para la configuración de concentradores y radios. Los túneles proporcionan una interfaz de acceso virtual independiente a demanda para cada sesión VPN.
1. El spoke inicia una solicitud de intercambio IKE con el hub para una conexión VPN.
2. El hub autentica el spoke.
3. El Cisco Secure Firewall Management Center asigna una plantilla virtual dinámica en el hub.
4. La plantilla virtual genera dinámicamente una interfaz de acceso virtual en el hub. Esta interfaz es única para la sesión VPN por radio.
5. El hub establece un túnel VTI dinámico con el spoke que utiliza la interfaz de acceso virtual.
6. El hub y el spoke intercambian tráfico a través del túnel que utiliza los protocolos de ruteo dinámico (BGP/OSPF/EIGRP) o con la función de redes protegidas (Multiple-Security Association VTI).
7. Las VTI dinámicas funcionan como cualquier otra interfaz de modo que usted puede aplicar QoS, reglas de firewall, protocolos de ruteo y otras funciones tan pronto como el túnel esté activo.
8. Se crea un único DVTI en el dispositivo HUB y varias interfaces de túnel estático para varios sitios remotos/radiales.
En este artículo se pueden probar BGP, OSPF y EIGRP sobre DVTI.

Nota: Cisco Secure Firewall ha añadido compatibilidad con DVTI en la versión 7.3 y actualmente solo admite una única DVTI según el ID de error de Cisco CSCwe13781.
Configurar
Diagrama de la red
Configuraciones
Configuración de Cisco Secure Firewall Hub
Configure la interfaz de origen del túnel físico.
interface GigabitEthernet0/0
nameif vlan2820
security-level 100
ip address 10.28.20.98 255.255.255.0 Configuración de la política IkEv2.
crypto ikev2 policy 1
encryption aes-256 aes-192 aes
integrity sha512 sha384 sha256 sha
group 21 20 14
prf sha256
lifetime seconds 86400Configure la política IPSEC y adjúntela a un nuevo perfil IPSEC.
crypto ipsec ikev2 ipsec-proposal VPN-LAB
protocol esp encryption aes-256 aes-192 aes
protocol esp integrity sha-512 sha-256 sha-1
crypto ipsec profile VPN-LAB-PROFILE
set ikev2 ipsec-proposal VPN-LAB
set security-association lifetime seconds 1000
Configure Virtual-template con el perfil IPSEC creado anteriormente y asígnelo a una interfaz de bucle invertido que proporcione la dirección IP para el DVTI.

Nota: Virtual-template se utiliza para configurar DVTI para túneles a demanda.
interface Loopback200
nameif DVTI-LOOPBACK
ip address 172.16.17.1 255.255.255.255
interface Virtual-Template1 type tunnel
nameif DVTI-HUB
ip unnumbered DVTI-LOOPBACK
tunnel source interface vlan2820
tunnel mode ipsec ipv4
tunnel protection ipsec profile FMC_IPSEC_PROFILE_2
Cree una interfaz de loopback secundaria para simular el tráfico de la red OnPREM detrás del hub.

Nota: omita este paso si tiene tráfico local detrás del hub.
interface Loopback100
nameif ON-PREM
ip address 192.168.9.1 255.255.255.255Configure el grupo de túnel.

Nota: La interfaz del conjunto de rutas del comando envía la dirección IP DVTI como una dirección IP estática al par.
tunnel-group 10.28.20.100 type ipsec-l2l
tunnel-group 10.28.20.100 ipsec-attributes
virtual-template 1
ikev2 remote-authentication pre-shared-key *****
ikev2 local-authentication pre-shared-key *****
ikev2 route set interfaceHabilite IKEv2 en la interfaz que crea el túnel.
crypto ikev2 enable vlan2820Configuración de radio de Cisco Secure Firewall
Configure la interfaz de origen del túnel físico.
interface GigabitEthernet0/0
nameif vlan2820
security-level 100
ip address 10.28.20.100 255.255.255.0 Configure la política IKEv2.
crypto ikev2 policy 1
encryption aes-256 aes-192 aes
integrity sha512 sha384 sha256 sha
group 21 20 14
prf sha256
lifetime seconds 86400Configure la política IPSEC y adjúntela a un nuevo perfil IPSEC.
crypto ipsec ikev2 ipsec-proposal VPN-LAB
protocol esp encryption aes-256 aes-192 aes
protocol esp integrity sha-512 sha-256 sha-1
crypto ipsec profile VPN-LAB-PROFILE
set ikev2 ipsec-proposal VPN-LAB
set security-association lifetime seconds 1000
Configure la interfaz de túnel virtual estática con el perfil IPSEC, creado previamente y asígnelo a una interfaz de bucle invertido que proporcione la dirección IP no numerada.
interface Loopback200
nameif VTI-LOOPBACK
ip address 172.16.17.2 255.255.255.255
interface Tunnel2
nameif SVTI-SPOKE-3
ip unnumbered VTI-LOOPBACK
tunnel source interface vlan2820
tunnel destination 10.28.20.98
tunnel mode ipsec ipv4
tunnel protection ipsec profile VPN-LAB-PROFILECree una interfaz de loopback secundaria para simular el tráfico de la red LAN-REMOTE-1 detrás de spoke.
interface Loopback100
nameif LAN-REMOTE-1
ip address 192.168.7.1 255.255.255.255Configure el grupo de túnel.

Nota: La interfaz del conjunto de rutas del comando envía la dirección IP de SVTI como una dirección IP estática al par.
tunnel-group 10.28.20.98 type ipsec-l2l
tunnel-group 10.28.20.98 ipsec-attributes
ikev2 remote-authentication pre-shared-key *****
ikev2 local-authentication pre-shared-key *****
ikev2 route set interfaceHabilite IKEv2 en la interfaz que puede construir el túnel.
crypto ikev2 enable vlan2820Configurar OSPF
Configuración del hub

Nota: El comando Redistribute connected subnets se utiliza para anunciar la red OnPREM a los spokes vía OSPF. La redistribución puede ser diferente según el diseño.
router ospf 1
router-id 172.16.17.1
network 172.16.17.0 255.255.255.0 area 0
log-adj-changes
redistribute connected subnetsConfiguración de radio
router ospf 1
router-id 172.16.17.2
network 172.16.17.0 255.255.255.0 area 0
log-adj-changes
redistribute connected subnetsVerificar OSPF
Verificación del hub
ASAV2-hub# show ospf
Routing Process "ospf 1" with ID 172.16.17.1
Start time: 4d23h, Time elapsed: 3d04h
Supports only single TOS(TOS0) routes
Supports opaque LSA
Supports Link-local Signaling (LLS)
Supports area transit capability
Event-log enabled, Maximum number of events: 1000, Mode: cyclic
It is an autonomous system boundary router
Redistributing External Routes from,
connected, includes subnets in redistribution
Router is not originating router-LSAs with maximum metric
Initial SPF schedule delay 5000 msecs
Minimum hold time between two consecutive SPFs 10000 msecs
Maximum wait time between two consecutive SPFs 10000 msecs
Incremental-SPF disabled
Minimum LSA interval 5 secs
Minimum LSA arrival 1000 msecs
LSA group pacing timer 240 secs
Interface flood pacing timer 33 msecs
Retransmission pacing timer 66 msecs
Number of external LSA 5. Checksum Sum 0x39716
Number of opaque AS LSA 0. Checksum Sum 0x0
Number of DCbitless external and opaque AS LSA 0
Number of DoNotAge external and opaque AS LSA 0
Number of areas in this router is 1. 1 normal 0 stub 0 nssa
Number of areas transit capable is 0
External flood list length 0
IETF NSF helper support enabled
Cisco NSF helper support enabled
Reference bandwidth unit is 100 mbps
Area BACKBONE(0)
Number of interfaces in this area is 3 (1 loopback)
Area has no authentication
SPF algorithm last executed 2d04h ago
SPF algorithm executed 10 times
Area ranges are
Number of LSA 2. Checksum Sum 0x1c99f
Number of opaque link LSA 0. Checksum Sum 0x0
Number of DCbitless LSA 0
Number of indication LSA 0
Number of DoNotAge LSA 0
Flood list length 0
ASAV2-hub# show ospf neighbor
Neighbor ID Pri State Dead Time Address Interface
172.16.17.2 0 FULL/ - 0:00:39 172.16.17.2 DVTI-HUB_va11La tabla de ruteo en el hub ahora muestra la red LAN-REMOTE-1 vía OSPF.
ASAV2-hub# show route ospf
Codes: L - local, C - connected, S - static, R - RIP, M - mobile, B - BGP
D - EIGRP, EX - EIGRP external, O - OSPF, IA - OSPF inter area
N1 - OSPF NSSA external type 1, N2 - OSPF NSSA external type 2
E1 - OSPF external type 1, E2 - OSPF external type 2, V - VPN
i - IS-IS, su - IS-IS summary, L1 - IS-IS level-1, L2 - IS-IS level-2
ia - IS-IS inter area, * - candidate default, U - per-user static route
o - ODR, P - periodic downloaded static route, + - replicated route
SI - Static InterVRF, BI - BGP InterVRF
Gateway of last resort is 10.28.20.101 to network 0.0.0.0
O E2 192.168.7.0 255.255.255.255
[110/20] via 172.16.17.2, 2d04h, DVTI-HUB_va11Verificación de radio
ASAv-spoke-2# show ospf
Routing Process "ospf 1" with ID 172.16.17.2
Start time: 3w3d, Time elapsed: 3d04h
Supports only single TOS(TOS0) routes
Supports opaque LSA
Supports Link-local Signaling (LLS)
Supports area transit capability
Event-log enabled, Maximum number of events: 1000, Mode: cyclic
It is an autonomous system boundary router
Redistributing External Routes from,
connected, includes subnets in redistribution
Router is not originating router-LSAs with maximum metric
Initial SPF schedule delay 5000 msecs
Minimum hold time between two consecutive SPFs 10000 msecs
Maximum wait time between two consecutive SPFs 10000 msecs
Incremental-SPF disabled
Minimum LSA interval 5 secs
Minimum LSA arrival 1000 msecs
LSA group pacing timer 240 secs
Interface flood pacing timer 33 msecs
Retransmission pacing timer 66 msecs
Number of external LSA 4. Checksum Sum 0x37bc8
Number of opaque AS LSA 0. Checksum Sum 0x0
Number of DCbitless external and opaque AS LSA 0
Number of DoNotAge external and opaque AS LSA 0
Number of areas in this router is 1. 1 normal 0 stub 0 nssa
Number of areas transit capable is 0
External flood list length 0
IETF NSF helper support enabled
Cisco NSF helper support enabled
Reference bandwidth unit is 100 mbps
Area BACKBONE(0)
Number of interfaces in this area is 2 (1 loopback)
Area has no authentication
SPF algorithm last executed 2d04h ago
SPF algorithm executed 1 times
Area ranges are
Number of LSA 2. Checksum Sum 0x1fe9a
Number of opaque link LSA 0. Checksum Sum 0x0
Number of DCbitless LSA 0
Number of indication LSA 0
Number of DoNotAge LSA 0
Flood list length 0
ASAv-spoke-2# show ospf neighbor
Neighbor ID Pri State Dead Time Address Interface
172.16.17.1 0 FULL/ - 0:00:34 172.16.17.1 SVTI-SPOKE-3La tabla de ruteo en spoke ahora muestra la red OnPREM a través de OSPF.
ASAv-spoke-2# show route ospf
Codes: L - local, C - connected, S - static, R - RIP, M - mobile, B - BGP
D - EIGRP, EX - EIGRP external, O - OSPF, IA - OSPF inter area
N1 - OSPF NSSA external type 1, N2 - OSPF NSSA external type 2
E1 - OSPF external type 1, E2 - OSPF external type 2, V - VPN
i - IS-IS, su - IS-IS summary, L1 - IS-IS level-1, L2 - IS-IS level-2
ia - IS-IS inter area, * - candidate default, U - per-user static route
o - ODR, P - periodic downloaded static route, + - replicated route
SI - Static InterVRF, BI - BGP InterVRF
Gateway of last resort is 10.28.20.101 to network 0.0.0.0
O E2 192.168.9.1 255.255.255.255
[110/20] via 172.16.17.1, 2d04h, SVTI-SPOKE-3Ahora el LAN-REMOTE-1 de radio puede alcanzar OnPREM.
ASAv-spoke-2# ping LAN-REMOTE-1 192.168.9.1
Type escape sequence to abort.
Sending 5, 100-byte ICMP Echos to 192.168.9.1, timeout is 2 seconds:
!!!!!
Success rate is 100 percent (5/5), round-trip min/avg/max = 1/2/10 ms
ASAv-spoke-2# show crypto ipsec sa peer 10.28.20.98 | i cap|iden|spi
local ident (addr/mask/prot/port): (0.0.0.0/0.0.0.0/0/0)
remote ident (addr/mask/prot/port): (0.0.0.0/0.0.0.0/0/0)
#pkts encaps: 9, #pkts encrypt: 9, #pkts digest: 9
#pkts decaps: 9, #pkts decrypt: 9, #pkts verify: 9
#PMTUs sent: 0, #PMTUs rcvd: 0, #decapsulated frgs needing reassembly: 0
current outbound spi: 4BC1FF2C
current inbound spi : FB455CB8
spi: 0xFB455CB8 (4215626936)
spi: 0x4BC1FF2C (1271004972)Ahora el concentrador OnPREM puede alcanzar LAN-REMOTE-1.
ASAV2-hub# ping ON-PREM 192.168.7.1
Type escape sequence to abort.
Sending 5, 100-byte ICMP Echos to 192.168.7.1, timeout is 2 seconds:
!!!!!
Success rate is 100 percent (5/5), round-trip min/avg/max = 1/2/10 ms
ASAV2-hub# show crypto ipsec sa peer 10.28.20.100
peer address: 10.28.20.100
interface: DVTI-HUB_va12
Crypto map tag: DVTI-HUB_vtemplate_dyn_map, seq num: 1, local addr: 10.28.20.98
Protected vrf (ivrf): Global
local ident (addr/mask/prot/port): (0.0.0.0/0.0.0.0/0/0)
remote ident (addr/mask/prot/port): (0.0.0.0/0.0.0.0/0/0)
current_peer: 10.28.20.100
#pkts encaps: 15, #pkts encrypt: 15, #pkts digest: 15
#pkts decaps: 15, #pkts decrypt: 15, #pkts verify: 15
#pkts compressed: 0, #pkts decompressed: 0
#pkts not compressed: 15, #pkts comp failed: 0, #pkts decomp failed: 0
#pre-frag successes: 0, #pre-frag failures: 0, #fragments created: 0
#PMTUs sent: 0, #PMTUs rcvd: 0, #decapsulated frgs needing reassembly: 0
#TFC rcvd: 0, #TFC sent: 0
#Valid ICMP Errors rcvd: 0, #Invalid ICMP Errors rcvd: 0
#send errors: 0, #recv errors: 0
local crypto endpt.: 10.28.20.98/500, remote crypto endpt.: 10.28.20.100/500
path mtu 1500, ipsec overhead 94(44), media mtu 1500
PMTU time remaining (sec): 0, DF policy: copy-df
ICMP error validation: disabled, TFC packets: disabledConfiguración de EIGRP
Configuración del hub:
ASAV2-hub# sh run router
router eigrp 10
network 172.16.17.0 255.255.255.0
redistribute connectedConfiguración de radio:
ASAv-spoke-2# sh run router
router eigrp 10
network 172.16.17.0 255.255.255.0
redistribute connected
Ahora el LAN-REMOTE-1 de radio puede alcanzar OnPREM.
ASAv-spoke-2# ping LAN-REMOTE-1 192.168.9.1 rep 100
Type escape sequence to abort.
Sending 100, 100-byte ICMP Echos to 192.168.9.1, timeout is 2 seconds:
!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!
!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!
Success rate is 100 percent (100/100), round-trip min/avg/max = 1/2/10 ms
ASAv-spoke-2# show crypto ipsec sa peer 10.28.20.98 | i cap|iden|spi
local ident (addr/mask/prot/port): (0.0.0.0/0.0.0.0/0/0)
remote ident (addr/mask/prot/port): (0.0.0.0/0.0.0.0/0/0)
#pkts encaps: 102, #pkts encrypt: 102, #pkts digest: 102
#pkts decaps: 102, #pkts decrypt: 102, #pkts verify: 102
#PMTUs sent: 0, #PMTUs rcvd: 0, #decapsulated frgs needing reassembly: 0
current outbound spi: 3EED404C
current inbound spi : 646D2C0C
spi: 0x646D2C0C (1684876300)
spi: 0x3EED404C (1055735884)Ahora el concentrador OnPREM puede alcanzar LAN-REMOTE-1.
ASAV2-hub# ping ON-PREM 192.168.7.1 rep 100
Type escape sequence to abort.
Sending 100, 100-byte ICMP Echos to 192.168.7.1, timeout is 2 seconds:
!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!
!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!
Success rate is 100 percent (100/100), round-trip min/avg/max = 1/1/10 ms
ASAV2-hub# show crypto ipsec sa peer 10.28.20.100 | i cap|iden|spi
local ident (addr/mask/prot/port): (0.0.0.0/0.0.0.0/0/0)
remote ident (addr/mask/prot/port): (0.0.0.0/0.0.0.0/0/0)
#pkts encaps: 208, #pkts encrypt: 208, #pkts digest: 208
#pkts decaps: 208, #pkts decrypt: 208, #pkts verify: 208
#PMTUs sent: 0, #PMTUs rcvd: 0, #decapsulated frgs needing reassembly: 0
current outbound spi: 646D2C0C
current inbound spi : 3EED404C
spi: 0x3EED404C (1055735884)
spi: 0x646D2C0C (1684876300)Verificar EIGRP
Verificación del hub:
ASAV2-hub# show eigrp neighbors
EIGRP-IPv4 Neighbors for AS(10)
H Address Interface Hold Uptime SRTT RTO Q Seq
(sec) (ms) Cnt Num
0 172.16.17.2 DVTI-HUB_va12 12 00:02:01 8 200 0 4La tabla de ruteo en el hub ahora muestra la red LAN-REMOTE-1 vía EIGRP.
ASAV2-hub# show route eigrp
Codes: L - local, C - connected, S - static, R - RIP, M - mobile, B - BGP
D - EIGRP, EX - EIGRP external, O - OSPF, IA - OSPF inter area
N1 - OSPF NSSA external type 1, N2 - OSPF NSSA external type 2
E1 - OSPF external type 1, E2 - OSPF external type 2, V - VPN
i - IS-IS, su - IS-IS summary, L1 - IS-IS level-1, L2 - IS-IS level-2
ia - IS-IS inter area, * - candidate default, U - per-user static route
o - ODR, P - periodic downloaded static route, + - replicated route
SI - Static InterVRF, BI - BGP InterVRF
Gateway of last resort is 10.28.20.101 to network 0.0.0.0
D EX 192.168.7.1 255.255.255.255
[170/53760] via 172.16.17.2, 00:05:28, DVTI-HUB_va12Verificación por radio:
ASAv-spoke-2# show eigrp neighbors
EIGRP-IPv4 Neighbors for AS(10)
H Address Interface Hold Uptime SRTT RTO Q Seq
(sec) (ms) Cnt Num
0 172.16.17.1 SVTI-SPOKE-3 12 00:07:05 34 204 0 3La tabla de ruteo en spoke ahora muestra la red OnPREM vía EIGRP.
ASAv-spoke-2# show route eigrp
Codes: L - local, C - connected, S - static, R - RIP, M - mobile, B - BGP
D - EIGRP, EX - EIGRP external, O - OSPF, IA - OSPF inter area
N1 - OSPF NSSA external type 1, N2 - OSPF NSSA external type 2
E1 - OSPF external type 1, E2 - OSPF external type 2, V - VPN
i - IS-IS, su - IS-IS summary, L1 - IS-IS level-1, L2 - IS-IS level-2
ia - IS-IS inter area, * - candidate default, U - per-user static route
o - ODR, P - periodic downloaded static route, + - replicated route
SI - Static InterVRF, BI - BGP InterVRF
Gateway of last resort is 10.28.20.101 to network 0.0.0.0
D EX 192.168.9.1 255.255.255.255
[170/53760] via 172.16.17.1, 00:07:43, SVTI-SPOKE-3Configuración de BGP

Nota: Cuando las interfaces VTI estáticas o dinámicas se combinan con eBGP, asegúrese de que el valor del salto TTL sea más de uno si utiliza BGP.
Configuración del hub:
router bgp 100
bgp log-neighbor-changes
bgp bestpath compare-routerid
address-family ipv4 unicast
neighbor 172.16.17.2 remote-as 200
neighbor 172.16.17.2 ebgp-multihop 10
neighbor 172.16.17.2 activate
redistribute connected
no auto-summary
no synchronization
exit-address-familyConfiguración de radio
router bgp 200
bgp log-neighbor-changes
bgp bestpath compare-routerid
address-family ipv4 unicast
neighbor 172.16.17.1 remote-as 100
neighbor 172.16.17.1 ebgp-multihop 10
neighbor 172.16.17.1 activate
redistribute connected
no auto-summary
no synchronization
exit-address-familyVerificar BGP
Verificación del hub:
ASAV2-hub# show bgp neighbors
BGP neighbor is 172.16.17.2, context single_vf, remote AS 200, external link
BGP version 4, remote router ID 192.168.7.1
BGP state = Established, up for 00:05:28
Last read 00:00:01, last write 00:01:00, hold time is 180, keepalive interval is 60 seconds
Neighbor sessions:
1 active, is not multisession capable (disabled)
Neighbor capabilities:
Route refresh: advertised and received(new)
Four-octets ASN Capability: advertised and received
Address family IPv4 Unicast: advertised and received
Multisession Capability:
Message statistics:
InQ depth is 0
OutQ depth is 0
Sent Rcvd
Opens: 1 1
Notifications: 0 0
Updates: 2 2
Keepalives: 6 6
Route Refresh: 0 0
Total: 9 9
Default minimum time between advertisement runs is 30 seconds
For address family: IPv4 Unicast
Session: 172.16.17.2
BGP table version 7, neighbor version 7/0
Output queue size : 0
Index 1
1 update-group member
Sent Rcvd
Prefix activity: ---- ----
Prefixes Current: 3 3 (Consumes 240 bytes)
Prefixes Total: 3 3
Implicit Withdraw: 0 0
Explicit Withdraw: 0 0
Used as bestpath: n/a 2
Used as multipath: n/a 0
Outbound Inbound
Local Policy Denied Prefixes: -------- -------
Bestpath from this peer: 2 n/a
Total: 2 0
Number of NLRIs in the update sent: max 3, min 0
Address tracking is enabled, the RIB does have a route to 172.16.17.2
Connections established 1; dropped 0
Last reset never
External BGP neighbor may be up to 10 hops away.
Transport(tcp) path-mtu-discovery is enabled
Graceful-Restart is disabled
ASAV2-hub#
ASAV2-hub# sh run router
router bgp 100
bgp log-neighbor-changes
bgp bestpath compare-routerid
address-family ipv4 unicast
neighbor 172.16.17.2 remote-as 200
neighbor 172.16.17.2 ebgp-multihop 10
neighbor 172.16.17.2 activate
redistribute connected
no auto-summary
no synchronization
exit-address-family
!
ASAV2-hub# sh run all router
router bgp 100
bgp log-neighbor-changes
no bgp always-compare-med
no bgp asnotation dot
no bgp bestpath med
bgp bestpath compare-routerid
bgp default local-preference 100
no bgp deterministic-med
bgp enforce-first-as
bgp maxas-limit 0
bgp transport path-mtu-discovery
timers bgp 60 180 0
address-family ipv4 unicast
bgp scan-time 60
bgp nexthop trigger enable
bgp nexthop trigger delay 5
bgp aggregate-timer 30
neighbor 172.16.17.2 remote-as 200
neighbor 172.16.17.2 ebgp-multihop 10
neighbor 172.16.17.2 activate
no bgp redistribute-internal
no bgp soft-reconfig-backup
no bgp suppress-inactive
redistribute connected
distance bgp 20 200 200
no auto-summary
no synchronization
exit-address-family
! La tabla de ruteo en el hub ahora muestra la red LAN-REMOTE-1 vía BGP.
ASAV2-hub# show route bgp
Codes: L - local, C - connected, S - static, R - RIP, M - mobile, B - BGP
D - EIGRP, EX - EIGRP external, O - OSPF, IA - OSPF inter area
N1 - OSPF NSSA external type 1, N2 - OSPF NSSA external type 2
E1 - OSPF external type 1, E2 - OSPF external type 2, V - VPN
i - IS-IS, su - IS-IS summary, L1 - IS-IS level-1, L2 - IS-IS level-2
ia - IS-IS inter area, * - candidate default, U - per-user static route
o - ODR, P - periodic downloaded static route, + - replicated route
SI - Static InterVRF, BI - BGP InterVRF
Gateway of last resort is 10.28.20.101 to network 0.0.0.0
B 192.168.7.1 255.255.255.255 [20/0] via 172.16.17.2, 00:06:16
Verificación por radio:
ASAv-spoke-2# show bgp neighbors
BGP neighbor is 172.16.17.1, context single_vf, remote AS 100, external link
BGP version 4, remote router ID 192.168.9.1
BGP state = Established, up for 00:06:59
Last read 00:00:27, last write 00:00:20, hold time is 180, keepalive interval is 60 seconds
Neighbor sessions:
1 active, is not multisession capable (disabled)
Neighbor capabilities:
Route refresh: advertised and received(new)
Four-octets ASN Capability: advertised and received
Address family IPv4 Unicast: advertised and received
Multisession Capability:
Message statistics:
InQ depth is 0
OutQ depth is 0
Sent Rcvd
Opens: 1 1
Notifications: 0 0
Updates: 2 2
Keepalives: 7 8
Route Refresh: 0 0
Total: 10 11
Default minimum time between advertisement runs is 30 seconds
For address family: IPv4 Unicast
Session: 172.16.17.1
BGP table version 9, neighbor version 9/0
Output queue size : 0
Index 1
1 update-group member
Sent Rcvd
Prefix activity: ---- ----
Prefixes Current: 3 3 (Consumes 240 bytes)
Prefixes Total: 3 3
Implicit Withdraw: 0 0
Explicit Withdraw: 0 0
Used as bestpath: n/a 2
Used as multipath: n/a 0
Outbound Inbound
Local Policy Denied Prefixes: -------- -------
Bestpath from this peer: 3 n/a
Total: 3 0
Number of NLRIs in the update sent: max 3, min 0
Address tracking is enabled, the RIB does have a route to 172.16.17.1
Connections established 1; dropped 0
Last reset never
External BGP neighbor may be up to 10 hops away.
Transport(tcp) path-mtu-discovery is enabled
Graceful-Restart is disabledLa tabla de ruteo en spoke ahora muestra la red OnPREM vía BGP.
ASAv-spoke-2# show route bgp
Codes: L - local, C - connected, S - static, R - RIP, M - mobile, B - BGP
D - EIGRP, EX - EIGRP external, O - OSPF, IA - OSPF inter area
N1 - OSPF NSSA external type 1, N2 - OSPF NSSA external type 2
E1 - OSPF external type 1, E2 - OSPF external type 2, V - VPN
i - IS-IS, su - IS-IS summary, L1 - IS-IS level-1, L2 - IS-IS level-2
ia - IS-IS inter area, * - candidate default, U - per-user static route
o - ODR, P - periodic downloaded static route, + - replicated route
SI - Static InterVRF, BI - BGP InterVRF
Gateway of last resort is 10.28.20.101 to network 0.0.0.0
B 192.168.9.1 255.255.255.255 [20/0] via 172.16.17.1, 00:09:22Troubleshoot
Para resolver problemas de OSPF, utilice estos comandos debug y show:
debug ip ospf
debug ip ospf packet
debug ip ospf events
debug ip ospf hello
debug ip ospf adj
show ospf
show ospf neighbor
show ospf interface Para resolver problemas de EIGRP, utilice estos debugs y comandos show:
debug ip eigrp
debug ip eigrp neighbor
debug ip eigrp notifications
show eigrp
show eigrp
show eigrp interfaces show eigrp neighbors show eigrp topology
Para resolver problemas de BGP, utilice estos debugs y los comandos show:.
debug ip bgp all
debug ip bgp updates
debug ip bgp events
show bgp
show bgp summary
show bgp neighbors Para resolver problemas de IKEv2, utilice estos comandos debug y show:
debug crypto ikev2 protocol 255
debug crypto ikev2 platform 255
debug crypto ipsec 255Información Relacionada
Historial de revisiones
| Revisión | Fecha de publicación | Comentarios |
|---|---|---|
1.0 |
31-Mar-2023 |
Versión inicial |
Con la colaboración de ingenieros de Cisco
- Alan Omar Garcia MarchanCisco HTTS Engineer
Contacte a Cisco
- Abrir un caso de soporte

- (Requiere un Cisco Service Contract)
 Comentarios
Comentarios