Configure Phase-3 Hierarchical DMVPN with Multi-Subnet Spokes
Available Languages
Bias-Free Language
The documentation set for this product strives to use bias-free language. For the purposes of this documentation set, bias-free is defined as language that does not imply discrimination based on age, disability, gender, racial identity, ethnic identity, sexual orientation, socioeconomic status, and intersectionality. Exceptions may be present in the documentation due to language that is hardcoded in the user interfaces of the product software, language used based on RFP documentation, or language that is used by a referenced third-party product. Learn more about how Cisco is using Inclusive Language.
Contents
Introduction
This document provides information about how to configure a Phase-3 Hierarchical Dynamic Multipoint VPN (DMVPN) with multi-subnet spokes.
Prerequisites
Requirements
Cisco recommends that you have knowledge of these topics:
Note: For hierarchical DMVPN with multi-subnet spokes, ensure that the routers have the bug fix of CSCug42027. With routers running IOS version without the fix of CSCug42027 , once the spoke to spoke tunnel is formed between the spokes in different subnets, the spoke to spoke traffic fails.
CSCug42027 is resolved in the following IOS and IOS-XE versions:
- 15.3(3)S / 3.10 and later.
- 15.4(3)M and later.
- 15.4(1)T and later.
Components Used
The information in this document is based on these hardware and software versions:
- Cisco 2911 Integrated Services Routers running Cisco IOS® Version 15.5(2)T
The information in this document was created from the devices in a specific lab environment. All of the devices used in this document started with a cleared (default) configuration. If your network is live, make sure that you understand the potential impact of any command.
Background Information
Hierarchical setup (greater than one level) allows for more complex tree-based DMVPN network topologies. Tree-based topologies allow the capability to build DMVPN networks with regional hubs that are spokes of central hubs. This architecture allows the regional hub to handle the data and Next Hop Resolution Protocol (NHRP) control traffic for its regional spokes. However, it still allows spoke-to-spoke tunnels to be built between any spokes within the DMVPN network, whether they are in the same region or not. This architecture also allows the DMVPN network layout to more closely match regional or hierarchical data flow patterns.
Configure
In this section, you are presented with the information in order to configure the features described in this document.
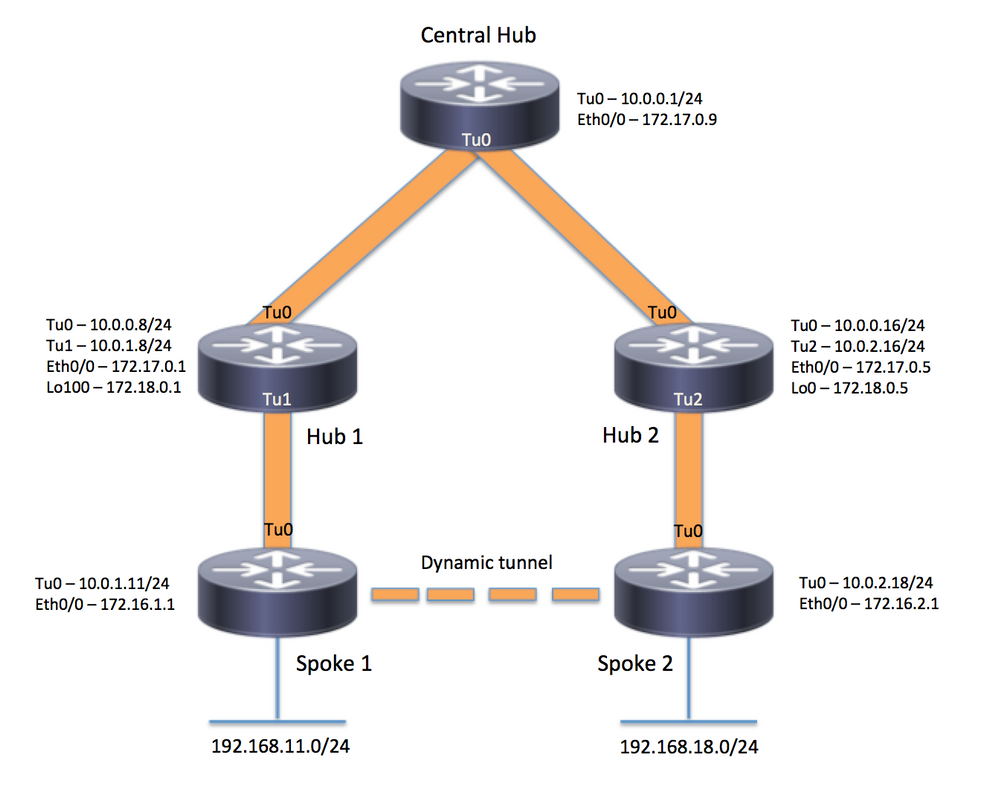
Network Diagram
Configurations
Note: Only the relevant sections of the configuration are included in this example.
Central Hub (Hub0)
version 15.5
service timestamps debug datetime msec
service timestamps log datetime msec
no service password-encryption
!
hostname central_hub
!
crypto isakmp policy 1
encr aes 256
hash sha256
authentication pre-share
group 2
crypto isakmp key cisco123 address 0.0.0.0
!
crypto ipsec transform-set transform-dmvpn esp-aes 256 esp-sha-hmac
mode transport
!
crypto ipsec profile profile-dmvpn
set transform-set transform-dmvpn
!
interface Loopback1
ip address 192.168.1.1 255.255.255.0
!
interface Tunnel0
bandwidth 1000
ip address 10.0.0.1 255.255.255.0
no ip redirects
ip mtu 1400
no ip split-horizon eigrp 1
ip nhrp authentication test
ip nhrp map multicast dynamic
ip nhrp network-id 100000
ip nhrp shortcut
ip nhrp redirect
ip summary-address eigrp 1 192.168.0.0 255.255.192.0
ip tcp adjust-mss 1360
tunnel source Ethernet0/0
tunnel mode gre multipoint
tunnel key 100000
tunnel protection ipsec profile profile-dmvpn
!
interface Ethernet0/0
ip address 172.17.0.9 255.255.255.252
!
router eigrp 1
network 10.0.0.0 0.0.0.255
network 192.168.1.0
!
ip route 0.0.0.0 0.0.0.0 172.17.0.10
!
end
Region 1 Hub (Hub 1)
version 15.5
service timestamps debug datetime msec
service timestamps log datetime msec
no service password-encryption
!
hostname hub_1
!
crypto isakmp policy 1
encr aes 256
hash sha256
authentication pre-share
group 2
crypto isakmp key cisco123 address 0.0.0.0
!
crypto ipsec transform-set transform-dmvpn esp-aes 256 esp-sha-hmac
mode transport
!
crypto ipsec profile profile-dmvpn
set transform-set transform-dmvpn
!
crypto ipsec profile profile-dmvpn-1
set transform-set transform-dmvpn
!
interface Loopback1
ip address 192.168.8.1 255.255.255.0
!
interface Loopback100
ip address 172.18.0.1 255.255.255.252
!
interface Tunnel0
bandwidth 1000
ip address 10.0.0.8 255.255.255.0
no ip redirects
ip mtu 1400
no ip split-horizon eigrp 1
ip nhrp authentication test
ip nhrp network-id 100000
ip nhrp nhs 10.0.0.1 nbma 172.17.0.9 multicast
ip nhrp shortcut
ip nhrp redirect
ip summary-address eigrp 1 192.168.8.0 255.255.248.0
ip tcp adjust-mss 1360
tunnel source Ethernet0/0
tunnel mode gre multipoint
tunnel key 100000
tunnel protection ipsec profile profile-dmvpn
!
interface Tunnel1
bandwidth 1000
ip address 10.0.1.8 255.255.255.0
no ip redirects
ip mtu 1400
ip nhrp authentication test
ip nhrp map multicast dynamic
ip nhrp network-id 100000
ip nhrp redirect
ip summary-address eigrp 1 192.168.8.0 255.255.248.0
ip summary-address eigrp 1 192.168.100.0 255.255.252.0
ip tcp adjust-mss 1360
tunnel source Loopback100
tunnel mode gre multipoint
tunnel key 100000
tunnel protection ipsec profile profile-dmvpn-1
!
interface Ethernet0/0
ip address 172.17.0.1 255.255.255.252
!
router eigrp 1
network 10.0.0.0 0.0.0.255
network 10.0.1.0 0.0.0.255
network 192.168.8.0
!
ip route 0.0.0.0 0.0.0.0 172.17.0.2
!
end
Region 2 Hub (Hub 2)
version 15.5
service timestamps debug datetime msec
service timestamps log datetime msec
no service password-encryption
!
hostname hub_2
!
crypto isakmp policy 1
encr aes 256
hash sha256
authentication pre-share
group 2
crypto isakmp key cisco123 address 0.0.0.0
!
crypto ipsec transform-set transform-dmvpn esp-aes 256 esp-sha-hmac
mode transport
!
crypto ipsec profile profile-dmvpn
set transform-set transform-dmvpn
!
crypto ipsec profile profile-dmvpn-1
set transform-set transform-dmvpn
!
interface Loopback0
ip address 172.18.0.5 255.255.255.252
!
interface Loopback1
ip address 192.168.16.1 255.255.255.0
!
interface Tunnel0
bandwidth 1000
ip address 10.0.0.16 255.255.255.0
no ip redirects
ip mtu 1400
ip nhrp authentication test
ip nhrp network-id 100000
ip nhrp holdtime 360
ip nhrp nhs 10.0.0.1 nbma 172.17.0.9 multicast
ip nhrp shortcut
ip nhrp redirect
ip summary-address eigrp 1 192.168.16.0 255.255.248.0
tunnel source Ethernet0/0
tunnel mode gre multipoint
tunnel key 100000
tunnel protection ipsec profile profile-dmvpn
!
interface Tunnel2
bandwidth 1000
ip address 10.0.2.16 255.255.255.0
no ip redirects
ip mtu 1400
ip nhrp authentication test
ip nhrp map multicast dynamic
ip nhrp network-id 100000
ip nhrp holdtime 360
ip nhrp redirect
ip summary-address eigrp 1 192.168.16.0 255.255.248.0
ip summary-address eigrp 1 192.168.100.0 255.255.252.0
tunnel source Loopback0
tunnel mode gre multipoint
tunnel key 100000
tunnel protection ipsec profile profile-dmvpn-1
!
interface Ethernet0/0
ip address 172.17.0.5 255.255.255.252
!
router eigrp 1
network 10.0.0.0 0.0.0.255
network 10.0.2.0 0.0.0.255
network 192.168.16.0
!
ip route 0.0.0.0 0.0.0.0 172.17.0.6
!
end
Region 1 Spoke (Spoke1)
version 15.5
service timestamps debug datetime msec
service timestamps log datetime msec
no service password-encryption
!
hostname spoke_1
!
crypto isakmp policy 1
encr aes 256
hash sha256
authentication pre-share
group 2
crypto isakmp key cisco123 address 0.0.0.0
crypto isakmp keepalive 10
!
crypto ipsec transform-set transform-dmvpn esp-aes 256 esp-sha-hmac
mode transport
!
crypto ipsec profile profile-dmvpn
set transform-set transform-dmvpn
!
interface Loopback1
ip address 192.168.11.1 255.255.255.0
!
interface Tunnel0
bandwidth 1000
ip address 10.0.1.11 255.255.255.0
no ip redirects
ip mtu 1400
ip nhrp authentication test
ip nhrp network-id 100000
ip nhrp nhs 10.0.1.8 nbma 172.18.0.1 multicast
ip nhrp shortcut
ip tcp adjust-mss 1360
tunnel source Ethernet0/0
tunnel mode gre multipoint
tunnel key 100000
tunnel protection ipsec profile profile-dmvpn
!
interface Ethernet0/0
ip address 172.16.1.1 255.255.255.252
!
router eigrp 1
network 10.0.0.0 0.0.0.255
network 10.0.1.0 0.0.0.255
network 192.168.11.0
!
ip route 0.0.0.0 0.0.0.0 172.16.1.2
!
end
Region 2 Spoke (Spoke 2)
version 15.5
service timestamps debug datetime msec
service timestamps log datetime msec
no service password-encryption
!
hostname spoke_2
!
crypto isakmp policy 1
encr aes 256
hash sha256
authentication pre-share
group 2
crypto isakmp key cisco123 address 0.0.0.0
crypto isakmp keepalive 10
!
crypto ipsec transform-set transform-dmvpn esp-aes 256 esp-sha-hmac
mode transport
!
crypto ipsec profile profile-dmvpn
set transform-set transform-dmvpn
!
interface Loopback1
ip address 192.168.18.1 255.255.255.0
!
interface Tunnel0
bandwidth 1000
ip address 10.0.2.18 255.255.255.0
no ip redirects
ip mtu 1400
ip nhrp authentication test
ip nhrp network-id 100000
ip nhrp nhs 10.0.2.16 nbma 172.18.0.5 multicast
ip nhrp shortcut
ip tcp adjust-mss 1360
tunnel source Ethernet0/0
tunnel mode gre multipoint
tunnel key 100000
tunnel protection ipsec profile profile-dmvpn
!
interface Ethernet0/0
ip address 172.16.2.1 255.255.255.252
!
router eigrp 1
network 10.0.2.0 0.0.0.255
network 192.168.18.0
!
ip route 0.0.0.0 0.0.0.0 172.16.2.2
!
end
Understanding the Data and NHRP Packet Flow
This image shows the first data packet flow followed by the NHRP resolution request and reply flow:

First Data Packet Flow
Step 1. ICMP ping initiated from spoke 1, destination = 192.168.18.10, source = 192.168.11.1
- Route lookup is done for 192.168.18.10. As seen below, the next hop is 10.0.1.8 (tunnel address of Hub 1)
- NHRP cache lookup is done for destination 192.168.18.10 on Tunnel0, however, no entry is found at this stage.
- NHRP cache lookup is done for the next hop i.e. 10.0.1.8 on Tunnel0. As seen below, the entry is present and the crypto session is UP.
- The ICMP echo request packet is forwarded to the next hop i.e. Hub1 over the existing tunnel.
spoke_1#show ip route 192.168.18.10
Routing entry for 192.168.0.0/18, supernet
Known via "eigrp 1", distance 90, metric 5248000, type internal
Redistributing via eigrp 1
Last update from 10.0.1.8 on Tunnel0, 02:30:37 ago
Routing Descriptor Blocks:
* 10.0.1.8, from 10.0.1.8, 02:30:37 ago, via Tunnel0
Route metric is 5248000, traffic share count is 1
Total delay is 105000 microseconds, minimum bandwidth is 1000 Kbit
Reliability 255/255, minimum MTU 1400 bytes
Loading 1/255, Hops 2
spoke_1#show ip nhrp
10.0.1.8/32 via 10.0.1.8
Tunnel0 created 02:31:32, never expire
Type: static, Flags: used
NBMA address: 172.18.0.1
Step 2. ICMP packet received on Hub 1
- Route lookup is done for 192.168.18.10. The next hop is 10.0.0.1 (tunnel address of Hub 0).
- Since Hub1 is not the exit point, and the packet needs to be forwarded to another interface within the same DMVPN cloud, Hub 1 sends an NHRP indirection/redirect to Spoke 1.
- At the same time, the data packet is forwarded to Hub0.
*Apr 13 19:06:07.592: NHRP: Send Traffic Indication via Tunnel1 vrf 0, packet size: 96
*Apr 13 19:06:07.592: src: 10.0.1.8, dst: 192.168.11.1
*Apr 13 19:06:07.592: (F) afn: AF_IP(1), type: IP(800), hop: 255, ver: 1
*Apr 13 19:06:07.592: shtl: 4(NSAP), sstl: 0(NSAP)
*Apr 13 19:06:07.592: pktsz: 96 extoff: 68
*Apr 13 19:06:07.592: (M) traffic code: redirect(0)
*Apr 13 19:06:07.592: src NBMA: 172.18.0.1
*Apr 13 19:06:07.592: src protocol: 10.0.1.8, dst protocol: 192.168.11.1
*Apr 13 19:06:07.592: Contents of nhrp traffic indication packet:
*Apr 13 19:06:07.592: 45 00 00 64 00 01 00 00 FE 01 1E 3C C0 A8 0B 01
*Apr 13 19:06:07.592: C0 A8 12 0A 08 00 A1 C8 00 01 00
Step 3. ICMP packet received on Hub 0
- Route lookup is done for 192.168.18.10. The next hop is 10.0.0.16 (tunnel address of Hub2) on Tunnel0
- Since Hub 0 is not the exit point and packet needs to be forwarded back onto the same DMVPN cloud via the same interface, hence Hub 0 sends the NHRP indirection to Spoke 1 through Hub 1.
- The data packet is forwarded to Hub 2.
*Apr 13 19:06:07.591: NHRP: Send Traffic Indication via Tunnel0 vrf 0, packet size: 96
*Apr 13 19:06:07.591: src: 10.0.0.1, dst: 192.168.11.1
*Apr 13 19:06:07.591: (F) afn: AF_IP(1), type: IP(800), hop: 255, ver: 1
*Apr 13 19:06:07.591: shtl: 4(NSAP), sstl: 0(NSAP)
*Apr 13 19:06:07.591: pktsz: 96 extoff: 68
*Apr 13 19:06:07.591: (M) traffic code: redirect(0)
*Apr 13 19:06:07.591: src NBMA: 172.17.0.9
*Apr 13 19:06:07.591: src protocol: 10.0.0.1, dst protocol: 192.168.11.1
*Apr 13 19:06:07.592: Contents of nhrp traffic indication packet:
*Apr 13 19:06:07.592: 45 00 00 64 00 01 00 00 FD 01 1F 3C C0 A8 0B 01
*Apr 13 19:06:07.592: C0 A8 12 0A 08 00 A1 C8 00 01 00
Step 4. ICMP packet received on Hub 2
- Route lookup is done for 192.168.18.10. The next hop is 10.0.2.18 (tunnel address of Spoke2) on Tunnel2
- Since Hub 2 is not the exit point and the packet needs to be forwarded to another interface within the same DMVPN cloud, Hub 2 sends the NHRP indirection to Spoke 1 through Hub 0.
- The data packet is forwarded to Spoke 2.
*Apr 13 19:06:07.592: NHRP: Send Traffic Indication via Tunnel0 vrf 0, packet size: 96
*Apr 13 19:06:07.593: src: 10.0.0.16, dst: 192.168.11.1
*Apr 13 19:06:07.593: (F) afn: AF_IP(1), type: IP(800), hop: 255, ver: 1
*Apr 13 19:06:07.593: shtl: 4(NSAP), sstl: 0(NSAP)
*Apr 13 19:06:07.593: pktsz: 96 extoff: 68
*Apr 13 19:06:07.593: (M) traffic code: redirect(0)
*Apr 13 19:06:07.593: src NBMA: 172.17.0.5
*Apr 13 19:06:07.593: src protocol: 10.0.0.16, dst protocol: 192.168.11.1
*Apr 13 19:06:07.593: Contents of nhrp traffic indication packet:
*Apr 13 19:06:07.593: 45 00 00 64 00 01 00 00 FC 01 20 3C C0 A8 0B 01
*Apr 13 19:06:07.593: C0 A8 12 0A 08 00 A1 C8 00 01 00
Step 5. ICMP packet received on Spoke 2
Route lookup is done for 192.168.18.10 and it is a locally connected network. It forwards the ICMP request to the destination.
NHRP Resolution Request Flow
Spoke 1
- The NHRP indirection sent by Hub 1 for destination 192.168.18.10 is received.
- An incomplete NHRP cache entry for 192.168.18.10/32 is inserted.
- Route lookup is done for 192.168.18.10. The next hop is 10.0.1.8 (Hub 1) on Tunnel0
- NHRP cache lookup is done for next hop 10.0.1.8 on Tunnel0. An entry is found and the crypto socket is also up (i.e. tunnel exists)
- Spoke 1 sends NHRP resolution request for 192.168.18.10/32 to Hub 1 over the existing spoke to the regional hub1 tunnel.
*Apr 13 19:06:07.596: NHRP: Receive Traffic Indication via Tunnel0 vrf 0, packet size: 96
*Apr 13 19:06:07.596: (F) afn: AF_IP(1), type: IP(800), hop: 255, ver: 1
*Apr 13 19:06:07.596: shtl: 4(NSAP), sstl: 0(NSAP)
*Apr 13 19:06:07.596: pktsz: 96 extoff: 68
*Apr 13 19:06:07.596: (M) traffic code: redirect(0)
*Apr 13 19:06:07.596: src NBMA: 172.18.0.1
*Apr 13 19:06:07.596: src protocol: 10.0.1.8, dst protocol: 192.168.11.1
*Apr 13 19:06:07.596: Contents of nhrp traffic indication packet:
*Apr 13 19:06:07.596: 45 00 00 64 00 01 00 00 FE 01 1E 3C C0 A8 0B 01
*Apr 13 19:06:07.596: C0 A8 12 0A 08 00 A1 C8 00 01 00
*Apr 13 19:06:07.596: NHRP: Attempting to create instance PDB for (0x0)
*Apr 13 19:06:07.609: NHRP: Send Resolution Request via Tunnel0 vrf 0, packet size: 84
*Apr 13 19:06:07.609: src: 10.0.1.11, dst: 192.168.18.10
*Apr 13 19:06:07.609: (F) afn: AF_IP(1), type: IP(800), hop: 255, ver: 1
*Apr 13 19:06:07.609: shtl: 4(NSAP), sstl: 0(NSAP)
*Apr 13 19:06:07.609: pktsz: 84 extoff: 52
*Apr 13 19:06:07.609: (M) flags: "router auth src-stable nat ", reqid: 3
*Apr 13 19:06:07.609: src NBMA: 172.16.1.1
*Apr 13 19:06:07.609: src protocol: 10.0.1.11, dst protocol: 192.168.18.10
*Apr 13 19:06:07.609: (C-1) code: no error(0)
*Apr 13 19:06:07.609: prefix: 32, mtu: 17912, hd_time: 7200
*Apr 13 19:06:07.609: addr_len: 0(NSAP), subaddr_len: 0(NSAP), proto_len: 0, pref: 0
Hub 1
- The NHRP resolution request from Spoke 1 for destination 192.168.18.1/32 is received.
- Route lookup is done for 192.168.18.1. The next hop is 10.0.0.1 (Hub 0) on Tunnel0
- The NHRP network ID for ingress and egress is same and the local node is not the exit point.
- NHRP cache lookup is done for next hop 10.0.0.1 on Tunnel0, entry is found and the crypto socket is up (tunnel exists)
- Hub1 forwards NHRP resolution request for 192.168.18.10/32 to Hub 0 over the existing tunnel
*Apr 13 19:06:07.610: NHRP: Receive Resolution Request via Tunnel1 vrf 0, packet size: 84
*Apr 13 19:06:07.610: (F) afn: AF_IP(1), type: IP(800), hop: 255, ver: 1
*Apr 13 19:06:07.610: shtl: 4(NSAP), sstl: 0(NSAP)
*Apr 13 19:06:07.610: pktsz: 84 extoff: 52
*Apr 13 19:06:07.610: (M) flags: "router auth src-stable nat ", reqid: 3
*Apr 13 19:06:07.610: src NBMA: 172.16.1.1
*Apr 13 19:06:07.610: src protocol: 10.0.1.11, dst protocol: 192.168.18.10
*Apr 13 19:06:07.610: (C-1) code: no error(0)
*Apr 13 19:06:07.610: prefix: 32, mtu: 17912, hd_time: 7200
*Apr 13 19:06:07.610: addr_len: 0(NSAP), subaddr_len: 0(NSAP), proto_len: 0, pref: 0
*Apr 13 19:06:07.610: NHRP: Forwarding Resolution Request via Tunnel0 vrf 0, packet size: 104
*Apr 13 19:06:07.610: src: 10.0.0.8, dst: 192.168.18.10
*Apr 13 19:06:07.610: (F) afn: AF_IP(1), type: IP(800), hop: 254, ver: 1
*Apr 13 19:06:07.610: shtl: 4(NSAP), sstl: 0(NSAP)
*Apr 13 19:06:07.610: pktsz: 104 extoff: 52
*Apr 13 19:06:07.610: (M) flags: "router auth src-stable nat ", reqid: 3
*Apr 13 19:06:07.610: src NBMA: 172.16.1.1
*Apr 13 19:06:07.610: src protocol: 10.0.1.11, dst protocol: 192.168.18.10
*Apr 13 19:06:07.610: (C-1) code: no error(0)
*Apr 13 19:06:07.610: prefix: 32, mtu: 17912, hd_time: 7200
*Apr 13 19:06:07.610: addr_len: 0(NSAP), subaddr_len: 0(NSAP), proto_len: 0, pref: 0
Hub 0
- The NHRP resolution request is received for destination 192.168.18.1/32, forwarded by Hub 1.
- Route lookup is done for 192.168.18.1. The next hop is 10.0.0.16 (Hub 2) on Tunnel0
- The NHRP network ID for ingress and egress is same and the local node is not the exit point.
- NHRP cache lookup is done for next hop 10.0.0.16 on Tunnel0, entry is found and the crypto socket is up (tunnel exists)
- Hub 0 forwards the NHRP resolution request for 192.168.18.1/32 to Hub 2 over the existing tunnel.
*Apr 13 19:06:07.611: NHRP: Receive Resolution Request via Tunnel0 vrf 0, packet size: 104
*Apr 13 19:06:07.611: (F) afn: AF_IP(1), type: IP(800), hop: 254, ver: 1
*Apr 13 19:06:07.611: shtl: 4(NSAP), sstl: 0(NSAP)
*Apr 13 19:06:07.611: pktsz: 104 extoff: 52
*Apr 13 19:06:07.611: (M) flags: "router auth src-stable nat ", reqid: 3
*Apr 13 19:06:07.611: src NBMA: 172.16.1.1
*Apr 13 19:06:07.611: src protocol: 10.0.1.11, dst protocol: 192.168.18.10
*Apr 13 19:06:07.611: (C-1) code: no error(0)
*Apr 13 19:06:07.611: prefix: 32, mtu: 17912, hd_time: 7200
*Apr 13 19:06:07.611: addr_len: 0(NSAP), subaddr_len: 0(NSAP), proto_len: 0, pref: 0
*Apr 13 19:06:07.611: NHRP: Forwarding Resolution Request via Tunnel0 vrf 0, packet size: 124
*Apr 13 19:06:07.611: src: 10.0.0.1, dst: 192.168.18.10
*Apr 13 19:06:07.611: (F) afn: AF_IP(1), type: IP(800), hop: 253, ver: 1
*Apr 13 19:06:07.611: shtl: 4(NSAP), sstl: 0(NSAP)
*Apr 13 19:06:07.612: pktsz: 124 extoff: 52
*Apr 13 19:06:07.612: (M) flags: "router auth src-stable nat ", reqid: 3
*Apr 13 19:06:07.612: src NBMA: 172.16.1.1
*Apr 13 19:06:07.612: src protocol: 10.0.1.11, dst protocol: 192.168.18.10
*Apr 13 19:06:07.612: (C-1) code: no error(0)
*Apr 13 19:06:07.612: prefix: 32, mtu: 17912, hd_time: 7200
*Apr 13 19:06:07.612: addr_len: 0(NSAP), subaddr_len: 0(NSAP), proto_len: 0, pref: 0
Hub 2
- The NHRP resolution request is received from Spoke 1 for destination 192.168.18.10/32, forwarded by Hub 0
- Route lookup is done for 192.168.18.10, next hop is 10.0.2.18 (Spoke 2) on Tunnel2
- The NHRP network ID for ingress and egress is same and the local node is not the exit point.
- NHRP cache lookup is done for next hop 10.0.2.18 on Tunnel2, entry is found and crypto socket is up (tunnel exists)
- Hub 2 forwards the NHRP resolution request for 192.168.18.1/32 to Spoke 2 over the existing tunnel
*Apr 13 19:06:07.613: NHRP: Receive Resolution Request via Tunnel0 vrf 0, packet size: 124
*Apr 13 19:06:07.613: (F) afn: AF_IP(1), type: IP(800), hop: 253, ver: 1
*Apr 13 19:06:07.613: shtl: 4(NSAP), sstl: 0(NSAP)
*Apr 13 19:06:07.613: pktsz: 124 extoff: 52
*Apr 13 19:06:07.613: (M) flags: "router auth src-stable nat ", reqid: 3
*Apr 13 19:06:07.613: src NBMA: 172.16.1.1
*Apr 13 19:06:07.613: src protocol: 10.0.1.11, dst protocol: 192.168.18.10
*Apr 13 19:06:07.613: (C-1) code: no error(0)
*Apr 13 19:06:07.613: prefix: 32, mtu: 17912, hd_time: 7200
*Apr 13 19:06:07.613: addr_len: 0(NSAP), subaddr_len: 0(NSAP), proto_len: 0, pref: 0
*Apr 13 19:06:07.613: NHRP: Forwarding Resolution Request via Tunnel2 vrf 0, packet size: 144
*Apr 13 19:06:07.613: src: 10.0.2.16, dst: 192.168.18.10
*Apr 13 19:06:07.613: (F) afn: AF_IP(1), type: IP(800), hop: 252, ver: 1
*Apr 13 19:06:07.613: shtl: 4(NSAP), sstl: 0(NSAP)
*Apr 13 19:06:07.613: pktsz: 144 extoff: 52
*Apr 13 19:06:07.613: (M) flags: "router auth src-stable nat ", reqid: 3
*Apr 13 19:06:07.613: src NBMA: 172.16.1.1
*Apr 13 19:06:07.613: src protocol: 10.0.1.11, dst protocol: 192.168.18.10
*Apr 13 19:06:07.613: (C-1) code: no error(0)
*Apr 13 19:06:07.613: prefix: 32, mtu: 17912, hd_time: 7200
*Apr 13 19:06:07.613: addr_len: 0(NSAP), subaddr_len: 0(NSAP), proto_len: 0, pref: 0
Spoke 2
- The NHRP resolution request is received for destination 192.168.18.1/32, forwarded by Hub 2
- Route lookup is done for 192.168.18.10, which is a locally connected network.
- Spoke 2 is the exit point and it generates the resolution reply for 192.168.18.10, prefix /24
- Spoke 2 inserts the NHRP cache entry for 10.0.1.11 (Spoke 1) using information from NHRP resolution request.
- Spoke 2 initiates the VPN tunnel with remote endpoint = NBMA address of Spoke 1. The dynamic Spoke-Spoke tunnel is negotiated.
- Then Spoke 2 sends the NHRP resolution reply for 192.168.18.10/24 to Spoke 1 over the dynamic tunnel that was just built.
*Apr 13 19:06:07.613: NHRP: Receive Resolution Request via Tunnel0 vrf 0, packet size: 144
*Apr 13 19:06:07.613: (F) afn: AF_IP(1), type: IP(800), hop: 252, ver: 1
*Apr 13 19:06:07.613: shtl: 4(NSAP), sstl: 0(NSAP)
*Apr 13 19:06:07.613: pktsz: 144 extoff: 52
*Apr 13 19:06:07.613: (M) flags: "router auth src-stable nat ", reqid: 3
*Apr 13 19:06:07.613: src NBMA: 172.16.1.1
*Apr 13 19:06:07.613: src protocol: 10.0.1.11, dst protocol: 192.168.18.10
*Apr 13 19:06:07.614: (C-1) code: no error(0)
*Apr 13 19:06:07.614: prefix: 32, mtu: 17912, hd_time: 7200
*Apr 13 19:06:07.614: addr_len: 0(NSAP), subaddr_len: 0(NSAP), proto_len: 0, pref: 0
*Apr 13 19:06:07.672: NHRP: Send Resolution Reply via Tunnel0 vrf 0, packet size: 172
*Apr 13 19:06:07.672: src: 10.0.2.18, dst: 10.0.1.11
*Apr 13 19:06:07.672: (F) afn: AF_IP(1), type: IP(800), hop: 255, ver: 1
*Apr 13 19:06:07.672: shtl: 4(NSAP), sstl: 0(NSAP)
*Apr 13 19:06:07.672: pktsz: 172 extoff: 60
*Apr 13 19:06:07.672: (M) flags: "router auth dst-stable unique src-stable nat ", reqid: 3
*Apr 13 19:06:07.672: src NBMA: 172.16.1.1
*Apr 13 19:06:07.672: src protocol: 10.0.1.11, dst protocol: 192.168.18.10
*Apr 13 19:06:07.672: (C-1) code: no error(0)
*Apr 13 19:06:07.672: prefix: 24, mtu: 17912, hd_time: 7200
*Apr 13 19:06:07.672: addr_len: 4(NSAP), subaddr_len: 0(NSAP), proto_len: 4, pref: 0
*Apr 13 19:06:07.672: client NBMA: 172.16.2.1
*Apr 13 19:06:07.672: client protocol: 10.0.2.18
Spoke1
- The NHRP resolution reply is received from Spoke 2 for destination 192.168.18.10, prefix /24 over the dynamic tunnel.
- The NHRP cache entry for 192.168.18.0/24 is now updated with next hop = 10.0.2.18, NBMA = 172.16.2.1
- A NHRP route is added in the RIB for the 192.168.18.10 network, next hop = 10.0.2.18.
*Apr 13 19:06:07.675: NHRP: Receive Resolution Reply via Tunnel0 vrf 0, packet size: 232
*Apr 13 19:06:07.675: (F) afn: AF_IP(1), type: IP(800), hop: 252, ver: 1
*Apr 13 19:06:07.675: shtl: 4(NSAP), sstl: 0(NSAP)
*Apr 13 19:06:07.675: pktsz: 232 extoff: 60
*Apr 13 19:06:07.675: (M) flags: "router auth dst-stable unique src-stable nat ", reqid: 3
*Apr 13 19:06:07.675: src NBMA: 172.16.1.1
*Apr 13 19:06:07.675: src protocol: 10.0.1.11, dst protocol: 192.168.18.10
*Apr 13 19:06:07.675: (C-1) code: no error(0)
*Apr 13 19:06:07.675: prefix: 24, mtu: 17912, hd_time: 7200
*Apr 13 19:06:07.675: addr_len: 4(NSAP), subaddr_len: 0(NSAP), proto_len: 4, pref: 0
*Apr 13 19:06:07.675: client NBMA: 172.16.2.1
*Apr 13 19:06:07.675: client protocol: 10.0.2.18
*Apr 13 19:06:07.676: NHRP: Adding route entry for 192.168.18.0/24 () to RIB
*Apr 13 19:06:07.676: NHRP: Route addition to RIB Successful
*Apr 13 19:06:07.676: NHRP: Route watch started for 192.168.18.0/23
*Apr 13 19:06:07.676: NHRP: Adding route entry for 10.0.2.18/32 (Tunnel0) to RIB
*Apr 13 19:06:07.676: NHRP: Route addition to RIB Successful .
spoke_1#show ip route 192.168.18.10
Routing entry for 192.168.18.0/24
Known via "nhrp", distance 250, metric 1
Last update from 10.0.2.18 00:09:46 ago
Routing Descriptor Blocks:
* 10.0.2.18, from 10.0.2.18, 00:09:46 ago
Route metric is 1, traffic share count is 1
MPLS label: none
Verify
Note: The Cisco CLI Analyzer (registered customers only) supports certain show commands. Use the Cisco CLI Analyzer in order to view an analysis of show command output.
Before Spoke-Spoke Tunnel is Built i.e NHRP Shortcut Entry is Formed
spoke_1#show ip nhrp
10.0.1.8/32 via 10.0.1.8
Tunnel0 created 02:19:32, never expire
Type: static, Flags: used
NBMA address: 172.18.0.1
spoke_1#
spoke_1#show ip route next-hop-override
Codes: L - local, C - connected, S - static, R - RIP, M - mobile, B - BGP
D - EIGRP, EX - EIGRP external, O - OSPF, IA - OSPF inter area
N1 - OSPF NSSA external type 1, N2 - OSPF NSSA external type 2
E1 - OSPF external type 1, E2 - OSPF external type 2
i - IS-IS, su - IS-IS summary, L1 - IS-IS level-1, L2 - IS-IS level-2
ia - IS-IS inter area, * - candidate default, U - per-user static route
o - ODR, P - periodic downloaded static route, H - NHRP, l - LISP
a - application route
+ - replicated route, % - next hop override
Gateway of last resort is 172.16.1.2 to network 0.0.0.0
S* 0.0.0.0/0 [1/0] via 172.16.1.2
10.0.0.0/8 is variably subnetted, 4 subnets, 2 masks
D 10.0.0.0/24 [90/5120000] via 10.0.1.8, 02:20:14, Tunnel0
C 10.0.1.0/24 is directly connected, Tunnel0
L 10.0.1.11/32 is directly connected, Tunnel0
D 10.0.2.0/24 [90/6681600] via 10.0.1.8, 02:20:03, Tunnel0
172.16.0.0/16 is variably subnetted, 2 subnets, 2 masks
C 172.16.1.0/30 is directly connected, Ethernet0/0
L 172.16.1.1/32 is directly connected, Ethernet0/0
172.25.0.0/32 is subnetted, 1 subnets
C 172.25.179.254 is directly connected, Loopback0
D 192.168.0.0/18 [90/5248000] via 10.0.1.8, 02:20:03, Tunnel0 <<<< Summary route received from hub1
D 192.168.8.0/21 [90/3968000] via 10.0.1.8, 02:20:14, Tunnel0
192.168.11.0/24 is variably subnetted, 2 subnets, 2 masks
C 192.168.11.0/24 is directly connected, Loopback1
L 192.168.11.1/32 is directly connected, Loopback1
spoke_1#
spoke_1#show dmvpn detail
Legend: Attrb --> S - Static, D - Dynamic, I - Incomplete
N - NATed, L - Local, X - No Socket
T1 - Route Installed, T2 - Nexthop-override
C - CTS Capable
# Ent --> Number of NHRP entries with same NBMA peer
NHS Status: E --> Expecting Replies, R --> Responding, W --> Waiting
UpDn Time --> Up or Down Time for a Tunnel
==========================================================================
Interface Tunnel0 is up/up, Addr. is 10.0.1.11, VRF ""
Tunnel Src./Dest. addr: 172.16.1.1/MGRE, Tunnel VRF ""
Protocol/Transport: "multi-GRE/IP", Protect "profile-dmvpn"
Interface State Control: Disabled
nhrp event-publisher : Disabled
IPv4 NHS:
10.0.1.8 RE NBMA Address: 172.18.0.1 priority = 0 cluster = 0
Type:Spoke, Total NBMA Peers (v4/v6): 1
# Ent Peer NBMA Addr Peer Tunnel Add State UpDn Tm Attrb Target Network
----- --------------- --------------- ----- -------- ----- -----------------
1 172.18.0.1 10.0.1.8 UP 00:02:31 S 10.0.1.8/32 <<<< Tunnel to the regional hub 1
Crypto Session Details:
--------------------------------------------------------------------------------
Interface: Tunnel0
Session: [0xF5F94CC8]
Session ID: 0
IKEv1 SA: local 172.16.1.1/500 remote 172.18.0.1/500 Active <<<<< Crypto session to the regional hub 1
Capabilities:D connid:1019 lifetime:23:57:28
Crypto Session Status: UP-ACTIVE
fvrf: (none), Phase1_id: 172.18.0.1
IPSEC FLOW: permit 47 host 172.16.1.1 host 172.18.0.1
Active SAs: 2, origin: crypto map
Inbound: #pkts dec'ed 35 drop 0 life (KB/Sec) 4153195/3448
Outbound: #pkts enc'ed 35 drop 0 life (KB/Sec) 4153195/3448
Outbound SPI : 0xACACB658, transform : esp-256-aes esp-sha-hmac
Socket State: Open
Pending DMVPN Sessions:
spoke_1#
After Spoke-Spoke Dynamic Tunnel is Formed i.e. NHRP Shortcut Entry is Formed
spoke_1#show ip nhrp
10.0.1.8/32 via 10.0.1.8
Tunnel0 created 02:24:04, never expire
Type: static, Flags: used
NBMA address: 172.18.0.1
10.0.2.18/32 via 10.0.2.18 <<<<<<<<<<< The new NHRP cache entry for spoke 2 that was learnt
Tunnel0 created 00:01:41, expire 01:58:18
Type: dynamic, Flags: router used nhop rib
NBMA address: 172.16.2.1
192.168.11.0/24 via 10.0.1.11
Tunnel0 created 00:01:26, expire 01:58:33
Type: dynamic, Flags: router unique local
NBMA address: 172.16.1.1
(no-socket)
192.168.18.0/24 via 10.0.2.18 <<<<<<<<<<<<< New NHRP cache entry formed for the remote subnet behind spoke2 that was learnt
Tunnel0 created 00:01:41, expire 01:58:18
Type: dynamic, Flags: router rib
NBMA address: 172.16.2.1
spoke_1#
spoke_1#sh ip route next-hop-override
Codes: L - local, C - connected, S - static, R - RIP, M - mobile, B - BGP
D - EIGRP, EX - EIGRP external, O - OSPF, IA - OSPF inter area
N1 - OSPF NSSA external type 1, N2 - OSPF NSSA external type 2
E1 - OSPF external type 1, E2 - OSPF external type 2
i - IS-IS, su - IS-IS summary, L1 - IS-IS level-1, L2 - IS-IS level-2
ia - IS-IS inter area, * - candidate default, U - per-user static route
o - ODR, P - periodic downloaded static route, H - NHRP, l - LISP
a - application route
+ - replicated route, % - next hop override
Gateway of last resort is 172.16.1.2 to network 0.0.0.0
S* 0.0.0.0/0 [1/0] via 172.16.1.2
10.0.0.0/8 is variably subnetted, 5 subnets, 2 masks
D 10.0.0.0/24 [90/5120000] via 10.0.1.8, 02:23:57, Tunnel0
C 10.0.1.0/24 is directly connected, Tunnel0
L 10.0.1.11/32 is directly connected, Tunnel0
D 10.0.2.0/24 [90/6681600] via 10.0.1.8, 02:23:46, Tunnel0
H 10.0.2.18/32 is directly connected, 00:01:48, Tunnel0
172.16.0.0/16 is variably subnetted, 2 subnets, 2 masks
C 172.16.1.0/30 is directly connected, Ethernet0/0
L 172.16.1.1/32 is directly connected, Ethernet0/0
172.25.0.0/32 is subnetted, 1 subnets
C 172.25.179.254 is directly connected, Loopback0
D 192.168.0.0/18 [90/5248000] via 10.0.1.8, 02:23:46, Tunnel0
D 192.168.8.0/21 [90/3968000] via 10.0.1.8, 02:23:57, Tunnel0
192.168.11.0/24 is variably subnetted, 2 subnets, 2 masks
C 192.168.11.0/24 is directly connected, Loopback1
L 192.168.11.1/32 is directly connected, Loopback1
H 192.168.18.0/24 [250/1] via 10.0.2.18, 00:01:48
spoke_1#
spoke_1#sh dmvpn detail
Legend: Attrb --> S - Static, D - Dynamic, I - Incomplete
N - NATed, L - Local, X - No Socket
T1 - Route Installed, T2 - Nexthop-override
C - CTS Capable
# Ent --> Number of NHRP entries with same NBMA peer
NHS Status: E --> Expecting Replies, R --> Responding, W --> Waiting
UpDn Time --> Up or Down Time for a Tunnel
==========================================================================
Interface Tunnel0 is up/up, Addr. is 10.0.1.11, VRF ""
Tunnel Src./Dest. addr: 172.16.1.1/MGRE, Tunnel VRF ""
Protocol/Transport: "multi-GRE/IP", Protect "profile-dmvpn"
Interface State Control: Disabled
nhrp event-publisher : Disabled
IPv4 NHS:
10.0.1.8 RE NBMA Address: 172.18.0.1 priority = 0 cluster = 0
Type:Spoke, Total NBMA Peers (v4/v6): 3
# Ent Peer NBMA Addr Peer Tunnel Add State UpDn Tm Attrb Target Network
----- --------------- --------------- ----- -------- ----- -----------------
1 172.18.0.1 10.0.1.8 UP 00:05:44 S 10.0.1.8/32
2 172.16.2.1 10.0.2.18 UP 00:01:51 DT1 10.0.2.18/32 <<<< Entry for spoke2's tunnel
172.16.2.1 10.0.2.18 UP 00:01:51 DT1 192.168.18.0/24 <<<< Entry for the subnet behind spoke2 that was learnt
1 172.16.1.1 10.0.1.11 UP 00:01:37 DLX 192.168.11.0/24 <<<< Entry formed for the local subnet
Crypto Session Details:
--------------------------------------------------------------------------------
Interface: Tunnel0
Session: [0xF5F94DC0]
Session ID: 0
IKEv1 SA: local 172.16.1.1/500 remote 172.18.0.1/500 Active
Capabilities:D connid:1019 lifetime:23:54:15
Crypto Session Status: UP-ACTIVE
fvrf: (none), Phase1_id: 172.18.0.1
IPSEC FLOW: permit 47 host 172.16.1.1 host 172.18.0.1
Active SAs: 2, origin: crypto map
Inbound: #pkts dec'ed 8 drop 0 life (KB/Sec) 4153188/3255
Outbound: #pkts enc'ed 9 drop 0 life (KB/Sec) 4153188/3255
Outbound SPI : 0xACACB658, transform : esp-256-aes esp-sha-hmac
Socket State: Open
Interface: Tunnel0
Session: [0xF5F94CC8]
Session ID: 0
IKEv1 SA: local 172.16.1.1/500 remote 172.16.2.1/500 Active
Capabilities:D connid:1020 lifetime:23:58:08
Crypto Session Status: UP-ACTIVE
fvrf: (none), Phase1_id: 172.16.2.1
IPSEC FLOW: permit 47 host 172.16.1.1 host 172.16.2.1
Active SAs: 2, origin: crypto map
Inbound: #pkts dec'ed 10 drop 0 life (KB/Sec) 4185320/3488
Outbound: #pkts enc'ed 10 drop 0 life (KB/Sec) 4185318/3488
Outbound SPI : 0xCAD04C8B, transform : esp-256-aes esp-sha-hmac
Socket State: Open
Pending DMVPN Sessions:
Reason for local, (no-socket) NHRP cache entry seen above
Local Flag refers to NHRP mapping entries that are for networks local to this router (serviced by this router). These entries are created when this router answers an NHRP resolution request with this information and is used to store the tunnel IP address of all of the other NHRP nodes to which it has sent this information. If for some reason this router loses access to this local network (it can no longer service this network) it will send an NHRP purge message to all remote NHRP nodes listed in the 'local' entry (show ip nhrp detail) to tell the remote nodes to clear this information out of their NHRP mapping tables.
No socket is seen for NHRP mapping entries for which we do not need nor want to trigger IPsec to setup encryption.
spoke_1#sh ip nhrp 192.168.11.0 detail
192.168.11.0/24 via 10.0.1.11
Tunnel0 created 00:01:01, expire 01:58:58
Type: dynamic, Flags: router unique local
NBMA address: 172.16.1.1
(no-socket)
Requester: 10.0.2.18 Request ID: 2
Troubleshoot
This section provides the information you can use in order to troubleshoot your configuration.
Note: Refer to Important Information on Debug Commands before you use debug commands.
DMVPN troubleshooting involves troubleshooting at 4 layers in this order:
- Physical (NBMA or tunnel endpoint) Routing layer
- IPsec Encryption layer
- GRE Encapsulation layer
- Dynamic Routing Protocols layer
Before troubleshooting, it is better to run these commands:
!! Enable msec debug and log timestamps
service timestamps debug datetime msec
service timestamps log datetime msec
!! To help correlate the debug output with the show command outputs
terminal exec prompt timestamp
Physical (NBMA or tunnel endpoint) Routing layer
Check if you can ping from the hub to the spoke's NBMA address and from the spoke to the hub's NBMA address (from the output of show ip nhrp on the spoke). These pings should go directly out the physical interface, not through the DMVPN tunnel. If this doesn't work you need to check the routing and any firewalls between the hub and spoke routers.
IPSec Encryption Layer
Run the following commands to check the ISAKMP SAs and IPsec SAs between the NBMA addresses of the hub and spoke.
show crypto isakmp sa detail
show crypto ipsec sa peer <NBMA-address-peer>
These debugs can be enabled to troubleshoot the IPSec encryption layer issues:
!! Use the conditional debugs to restrict the debug output for a specific peer.
debug crypto condition peer ipv4 <NBMA address of the peer>
debug crypto isakmp
debug crypto ipsec
NHRP
The spoke send NHRP registration requests on a regular basis, every 1/3 NHRP holdtime (on spoke) or ip nhrp registration timeout <seconds> value. You can check on this on the spoke by running:
show ip nhrp nhs detail
show ip nhrp traffic
Use the above commands to check if the spoke is sending NHRP registration requests and getting replies from the hub.
To check if the hub has the NHRP mapping entry for the spoke in the NHRP cache on the hub, run this command:
show ip nhrp <spoke-tunnel-ip-address>
To troubleshoot NHRP related issues, these debugs can be used:
!! Enable conditional NHRP debugs
debug nhrp condition peer tunnel <tunnel address of the peer>
OR
debug nhrp condition peer nbma <nbma address of the peer>
debug nhrp
debug nhrp packet
Dynamic Routing Protocols Layer
Refer these documents depending on the dynamic routing protocol being used:
Related Information
Contributed by Cisco Engineers
- Nitin DhingraCisco TAC Engineer
- Rudresh VeerappajiCisco TAC Engineer
Contact Cisco
- Open a Support Case

- (Requires a Cisco Service Contract)
 Feedback
Feedback